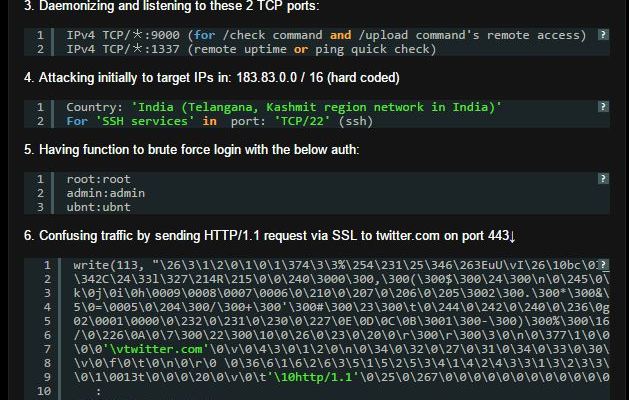
SWEET32 Attack: 3DES and Blowfish Ciphers Considered Insecure
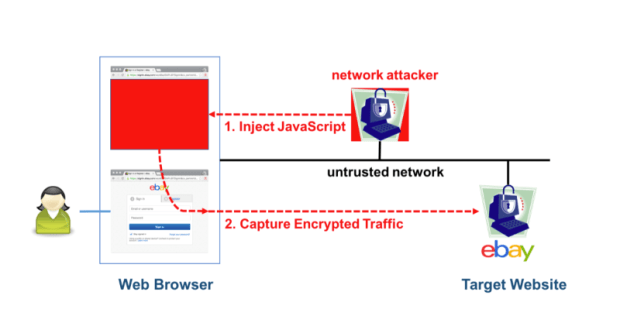
HTTPS and VPN traffic broken with new semi-practical attack. Two scientists from the French Institute for Research in Computer Science and Automation (INRIA) have published new research that details an attackRead More →