SAN storage products of Dell, Fujitsu, HP, Huawei, IBM, Brocade and Lenovo affected by 9 critical vulnerabilities
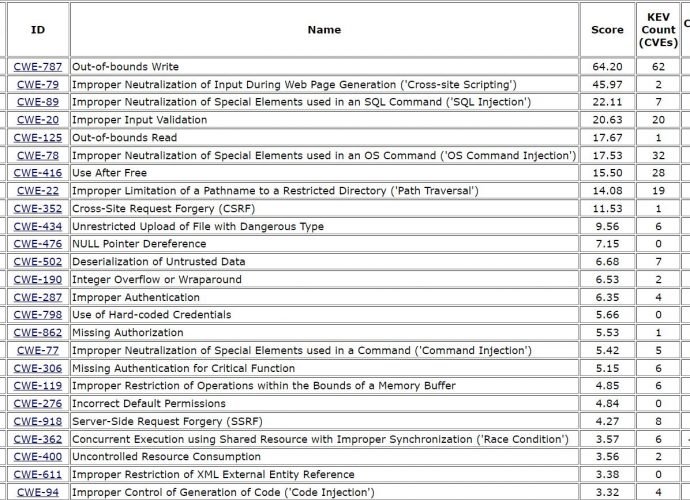
Broadcom published that software used by its storage networking company Brocade is affected by 9 important vulnerabilities, and the same vulnerabilities impact the SAN products of several major companies likeRead More →