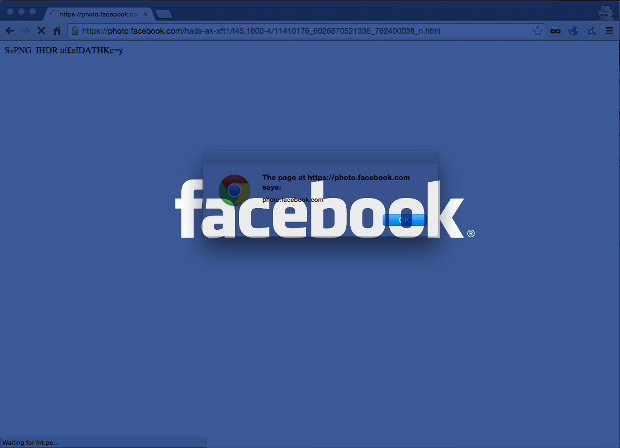
From Linux to Windows – New Family of Cross-Platform Desktop Backdoors Discovered
Recently we came across a new family of cross-platform backdoors for desktop environments. First we got the Linux variant, and with information extracted from its binary, we were able toRead More →