Windows and Linux Malware Linked to Chinese DDoS Tool
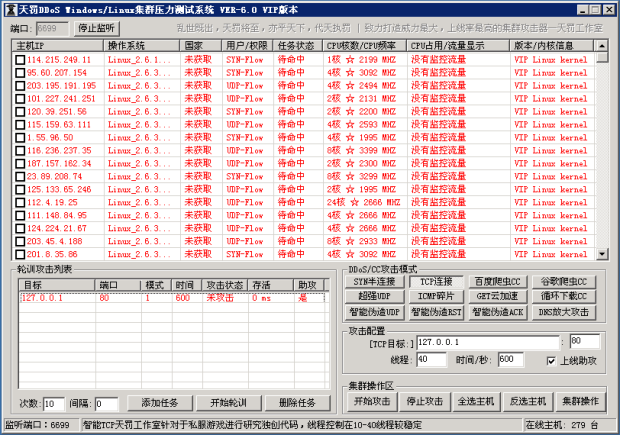
Malware was infecting machines, adding them to its botnet.Similar-looking malware targeting both Linux and Windows computers has been linked to a DDoSing toolkit sold by Chinese hackers via the ddos[.]tfRead More →