How the Internet of Things Got Hacked
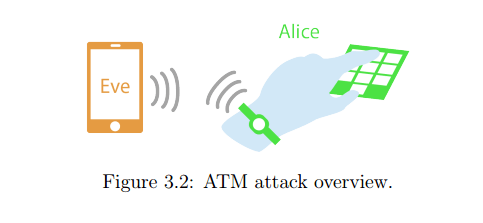
THERE WAS ONCE a time when people distinguished between cyberspace, the digital world of computers and hackers, and the flesh-and-blood reality known as meatspace. Anyone overwhelmed by the hackable perilsRead More →