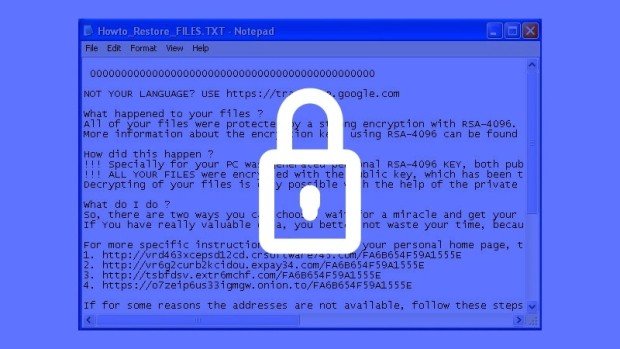
Intense Nemucod Malware Campaign Spreads Teslacrypt Ransomware
TeslaCrypt ransomware infections continue to surge. We reported last week about the first signs of a new TeslasCrypt ransomware campaign that was slowly starting to shape up. Now, after only aRead More →