Crypto e-mail service pays $6,000 ransom, gets taken out by DDoS anyway
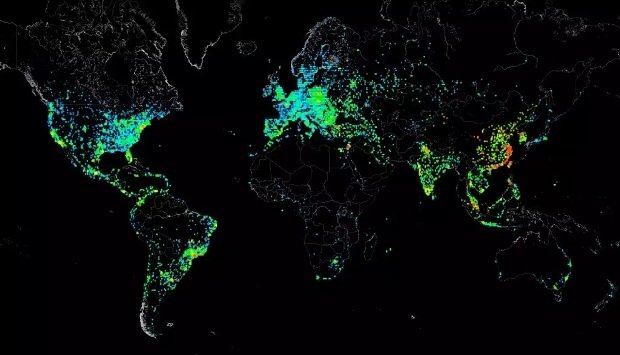
Follow-on attacks show capabilities “commonly possessed by state-sponsored actors.” A provider of end-to-end encrypted e-mail said it paid a ransom of almost $6,000 to stop highly advanced denial-of-service attacks thatRead More →