Earlier this month, exploit acquisition platform Zerodium debuted an iOS 9 bug bounty that would pay out up to three million dollars to hackers who managed to develop a browser-based untethered jailbreak for iOS 9, which it could then sell to clients interested in shelling out a lot of money to gain illicit access to iOS devices.
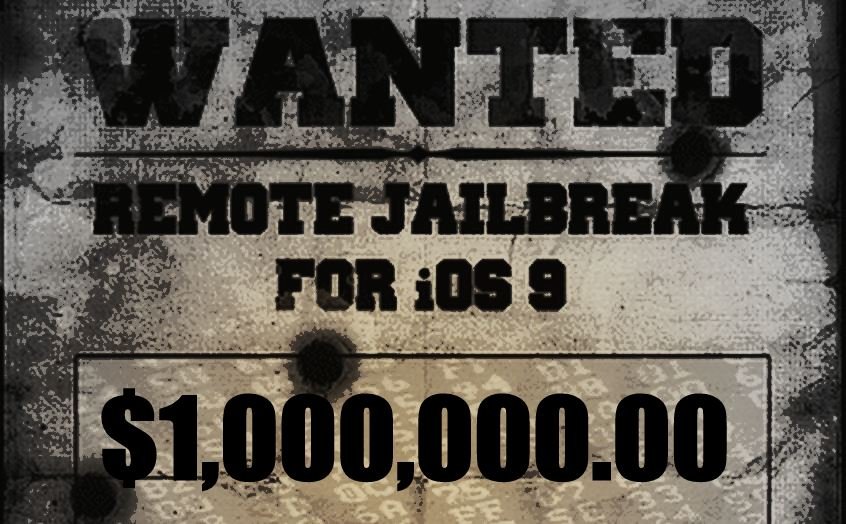
The contest expired at the end of October, and Zerodium today announced one hacking team had successfully created a browser-based jailbreak for iOS 9.1 and iOS 9.2, the latest versions of iOS 9, earning $1 million.
Zerodium foundar Chaouki Bekrar told Wired that the exploit developed by the hackers will be given to its customers, which include major technology, finance, and defense corporations, along with government agencies. The contest rules required the exploit to be achievable remotely without requiring user interaction beyond reading a text message or visiting a website via Chrome or Safari on an iOS device.
Bekrar confirmed that Zerodium plans to reveal the technical details of the technique to its customers, whom the company has described as “major corporations in defense, technology, and finance” seeking zero-day attack protection as well as “government organizations in need of specific and tailored cybersecurity capabilities.”
Because it’s selling the jailbreak (“likely” to U.S. customers only), Zerodium does not plan to report the vulnerabilities in the operating system to Apple, though Bekrar says the company may share the details at a later date. The jailbreak also won’t be provided to the general public, but Bekrar says Zerodium announced the results of the contest to remind people that while iOS security is “very hardened,” it’s not unbreakable.
Source: macrumors.com

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











