A stored XSS vulnerability was identified and reported by Bitdefender’s staff to PayPal, one that could have been easily used by hackers as an entry point for further attacks.
We recently posted an article based on Jack Leonard’s “How XSS Attacks Work” infographic. And as we explained in that post, the difference between reflective and stored XSS attacks lies in the fact that, in reflective XSS vulnerabilities, an attacker exploits the server’s HTTP request-response loop with maliciously crafted URLs. This type of attacks only affect one user at a time, usually the user accessing that URL.
The problem with stored XSS attacks is that attackers use malicious crafted URLs to store their XSS exploit code on the server. This is in the form of a blog comment, a forum post, a database entry, and so on. When any user accesses a page where the XSS attack code is “stored,” that particular snippet of code is loaded in his/her browser and executed.
This is why this kind of attacks are way more dangerous than reflected XSS, and this is exactly what Bitdefender’s team has uncovered on PayPal’s customer dashboard, and more specifically in the Request Money -> Create Invoice section.
The stored XSS vulnerability was found in PayPal Create Invoice section
According to Bitdefender’s Liviu Arsene, the problem was found in how PayPal’s system encrypted URLs when users uploaded files in their Create Invoice section.
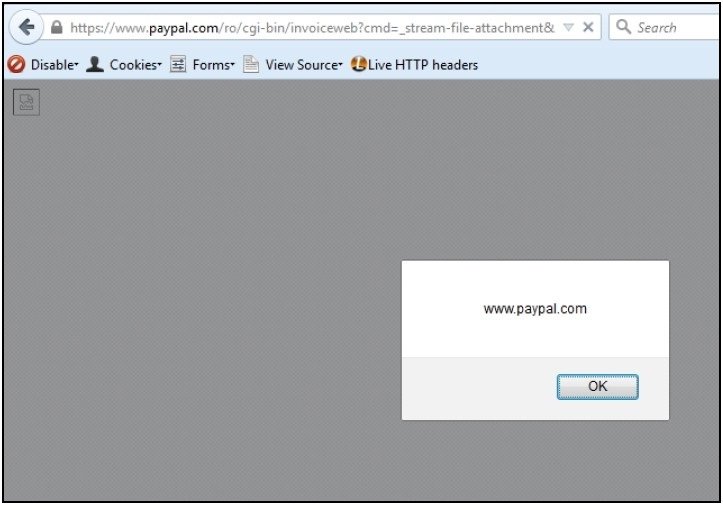
In Bitdefender’s proof-of-concept, its security researchers have performed a CBC (Cipher Block Chaining) attack on the URL that pulled uploaded files from PayPal’s servers, on a previously uploaded HTML-formatted XML file.
“Because the ‘id’ parameter for each uploaded file takes the value of a ciphertext encoded in base64 and uses the CBC (Cipher Block Chaining) ciphering mode,” said Bitdefender, “The attack involved changing a series of bytes from each cipher block in order to force the PayPal server to execute the malicious payload.”
The XSS could have been weaponized to deliver malicious content
In the end, by using this stored XSS vulnerability, attackers would have been able to make PayPal output files in the form of “~test.bat” instead of invoices.
Attackers could have controlled the content of these files, delivering malware or using them as an entry point for further attacks.
Since the files came from PayPal’s servers, non-technical users would have had no hesitation in launching the .bat files, thinking it was an invoice stored in some “weird” format.
The vulnerability could have been exploited via Firefox browsers only because PayPal servers would not set any Content Disposition parameter in their reply form when the User Agent string contained the word “Firefox.”
According to Bitdefender, this type of attack was never detected as being used in the wild.
The famous antivirus maker has worked closely with the PayPal staff and the vulnerability has been properly disclosed and fixed. Bitdefender sources told Softpedia that this XSS vulnerability was reported to PayPal at the start of May.
Just over a week ago, PayPal also fixed another stored XSS vulnerability, one which could have exposed personal user details to attackers.
Source:https://news.softpedia.com/

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.