Putrid Piper picked apart a packet for just $15.
KU Leuven Phd student Mathy Vanhoef has smashed conventional wireless security thought by creating continual, targeted and virtually indefensible stealth jamming of WiFi, Bluetooth, and Zigbee networks, and tampering with encrypted traffic, with little more than a $15 dongle.
The wireless security boffin presented his work at the BruCon conference last week and revealed his weapon of choice is a bargain WiFi dongle bought off Amazon that, when paired with a Raspberry Pi and a small amplifier, can block 2.4Ghz transmissions for up to 120 metres.
“You do not need these expensive devices – you can use a very cheap Wi-Fi dongle,” Vanhoef says.
“You have (in the 2.4Ghz spectrum) home automation systems, home security systems, sometimes industrial control systems, fancy baby monitors, car locks – and this is not wild speculation, if jammers are available thieves will use them.
“As a defender you should be at least able to detect these attacks.”
The Wi-Fi weakness lies in the fact that Wi-Fi assumes all devices play fair and will wait for transmissions to clear before sending packets. This scheme works well to ensure bandwidth is equally shared among devices, but it gives ample play room for selfish attackers.
The targeted and continuous Wi-Fi jamming requires a few steps. Attackers must first disable their dongle’s backoff wait time (SIFS) designed to give Wi-Fi devices time to cleanly re-enter transmission mode, a feat possible by tinkering with memory mapped registers within firmware. Vanhoef says the manipulation is easy enough.
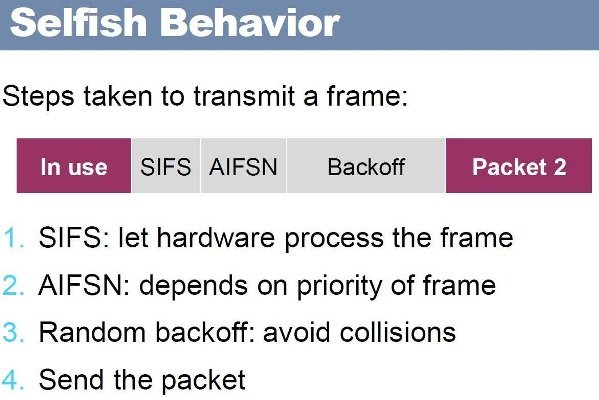
Attackers can also abuse WiFi etiquette regarding collisions by changing their bitrate so that it is lower than that of their rivals and therefore will be processed first.
Vanhoef says continual jamming is possible using the dongles if carrier sense is disabled and a frame is set to be continually resent. This combined means that devices will wait for the attacker’s initial frame to be sent, when in fact it simply infinitely loops. The attack cannot be stopped and therefore the hacker says he will not release the code but is happy to supply it to legitimate researchers.
TKIP flip
Vanhoef also showed how frames can be manipulated or dropped and/or recovered from still widely-used WPA-TKIP encrypted networks. Here attackers can intercept traffic by cloning a target access point and using the same MAC address on a different channel.
He says TKIP is still commonly used where devices include it for legacy support. In tests of more than 9000 networks two thirds supported were using TKIP for broadcast traffic.
The attacks work in part because MIC failure reports can be captured. This means the reports sent to warn access points of attacks and to cease transmissions never arrive making the attacks effectively stealth.
Peter Piper picked apart a packet
Wi-Fi wreckers wanting to jam specific packets on the 2.4 Ghz or 5 Ghz spectra can reconstruct the header of a packet for source and destination information and stuff dummy information in the remainder.
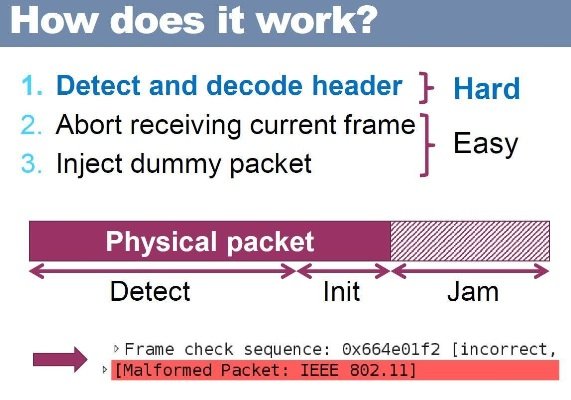
This process of decoding the header is not easy nor 100 percent reliable and works for medium-to-large packets which allow enough time for decoding.
It is however equally a tool useful to defenders who can use the attacks to turn tables on jammers by hitting their offending access points, VanHoef says.
Specific Wi-Fi jamming is made simple using VanHoef’s “basically” plug and play virtual machine.
Source:https://www.theregister.co.uk/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











