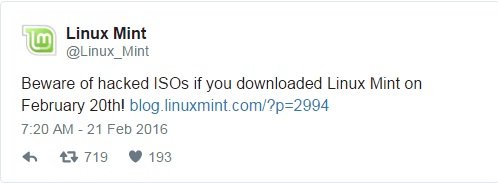
The Linux Mint website had been hacked, on Saturday, intruders were able to compromise it and serve malicious ISO of Linux Mint 17.3 Cinnamon edition.
The Linux Mint website had been hacked, on Saturday 20th, February, intruders were able to compromise the website serving malicious ISO of Linux Mint 17.3 Cinnamon edition.
The disconcerting announcement was made by Clement Lefebvre, the head of the Linux Mint project. Lefebvre explained that the webLinux Mint website had been compromised and that the hackers used it to distribute a malicious ISO of Linux Mint 17.3 Cinnamon edition.
“I’m sorry I have to come with bad news. We were exposed to an intrusion today. It was brief and it shouldn’t impact many people, but if it impacts you, it’s very important you read the information below. What happened?
What happened?
Hackers made a modified Linux Mint ISO, with a backdoor in it, and managed to hack our website to point to it.” wrote Clement Lefebvre.
Users that downloaded the Linux Mint 17.3 Cinnamon edition prior to Saturday, or any other version/flavour (including Mint 17.3 Cinnamon via torrent or direct HTTP link), are not affected.
The operators behind the website of the Linux distribution have sanitized it.

Lefebvre urges the users to check the MD5 digest of the downloaded ISOs in order to discover any modification to the legitimate software.
“If you still have the ISO file, check its MD5 signature with the command “md5sum yourfile.iso” (where yourfile.iso is the name of the ISO).” continues the post.
Below the list of valid signatures:
6e7f7e03500747c6c3bfece2c9c8394f linuxmint-17.3-cinnamon-32bit.iso
e71a2aad8b58605e906dbea444dc4983 linuxmint-17.3-cinnamon-64bit.iso
30fef1aa1134c5f3778c77c4417f7238 linuxmint-17.3-cinnamon-nocodecs-32bit.iso
3406350a87c201cdca0927b1bc7c2ccd linuxmint-17.3-cinnamon-nocodecs-64bit.iso
df38af96e99726bb0a1ef3e5cd47563d linuxmint-17.3-cinnamon-oem-64bit.iso
“If you still have the burnt DVD or USB stick, boot a computer or a virtual machine offline (turn off your router if in doubt) with it and let it load the live session.
Once in the live session, if there is a file in /var/lib/man.cy, then this is an infected ISO.”
If you have an infected ISO delete it, trash discs used to burn the ISO, and format USB sticks where the ISO was burnt.
If you have installed Linux Mint from an infected ISO follow these steps:
- Take the computer offline.
- Backup personal data.
- Reinstall the OS (with a clean ISO) or format the partition.
- And change passwords to sites you used – especially email accounts.
Who is behind the attack?
The hacked ISOs are hosted on a server with the IP 5.104.175.212 and the backdoor connects to the absentvodka.com domain.
The IP and the domain used in the attack lead to 3 people located in Sofia, Bulgaria. It is not clear the roles in the attack..
“What we don’t know is the motivation behind this attack. If more efforts are made to attack our project and if the goal is to hurt us, we’ll get in touch with authorities and security firms to confront the people behind this.” added Clement Lefebvre.
Source:https://securityaffairs.co/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.