A bug in the iOS WebView component allows an attacker to force someone’s iPhone to dial any number, while also locking the user’s interface for a few moments, preventing him to cancel the outgoing call.
Security researcher Collin Mulliner discovered a first variant of this issue in 2008, affecting Apple’s mobile Safari browser, which the Cupertino tech giant fixed with the release of iOS 3.0.
The researcher revisited his bug over the past two weeks, after the recent arrest of an Arizona teenager who exploited a similar bug and inadvertently caused a flood of hang-up calls to 911 emergency call centers across the US.
The Arizona teen had created a JavaScript-based exploit that, he says, leveraged a new iOS bug to force the user’s iPhone to redial a specific number. The misguided teen says he erroneously shared online a weaponized version of this bug that made calls to 911, instead of a random test number.
2008 Safari bug found in current iOS WebView distributions
Mulliner thinks that he might have identified how
Twitter, LinkedIn, Facebook, or Pocket, use this component to open links inside their iOS apps, without opening an external browser such as Safari, Firefox, or Chrome.
WebView having problems with TEL (telephone) HTML links
The issue is in how the WebView component (mis)handles telephone links (TEL URIs such as tel:< phone number >) embedded in web pages.
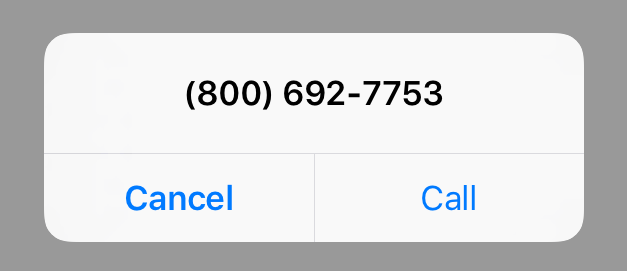
If the user clicks on the link, in WebView, the phone automatically dials the number. If the attacker redirects the user to a page that uses a meta-refresh tag to reload the page with a new URL, of the number he wants to dial, the phone automatically dials the phone number, even if the user clicked on a seemingly innocent link.
In Safari, where Apple fixed the issue, the browser asks the user via a popup if he wants to call the number.
Bug “extra” exploit prevents users from canceling calls
Despite the auto-dialing behavior, Mulliner says that users can still cancel these calls. The bad news is that an attacker could use repeated page refreshes, to force the user’s WebView component to spawn additional components.
This is possible thanks to URI binding, the practice of automatically opening specific links with predetermined apps, such as the default SMS app for SMS: URLs or iTunes via the itms-apps: URL.
Opening multiple apps in a short time, while also initiating a call, freezes the user’s iPhone UI, and he can’t cancel the call.
Mulliner also recorded two proof-of-concept videos showing the bug in action for the Twitter and LinkedIn iOS apps, which use WebView components to open in-app links.
the teen carried out his attacks. The researcher discovered that the iOS WebView component suffers from the same bug he discovered in Safari in 2008.
The iOS WebView component is a stripped down browser that developers integrate with their apps to provide an in-app web page viewing component.
Despite the bug being present in the WebView component, app makers can take precautionary measures to protect their users until Apple fixes iOS’ WebView module.
Bug reported to Apple
The researchers says he reported the issue to Twitter, who closed it as a duplicate without any explanation. LinkedIn ran a private bug bounty program, and he couldn’t alert the company to this issues. He also informed Apple about the core WebView issue.
In a blog post on his site, Mulliner also raises concerns about the issue not being addressed in due time, by both Apple and iOS app makers.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











