The team at Cybereason released today a new tool that tries to help users stay safe from ransomware infections. Named RansomFree, this application can help users of Windows 7, 8 and 10, and Windows Server 2010 R2 and 2008 R2 PCs.
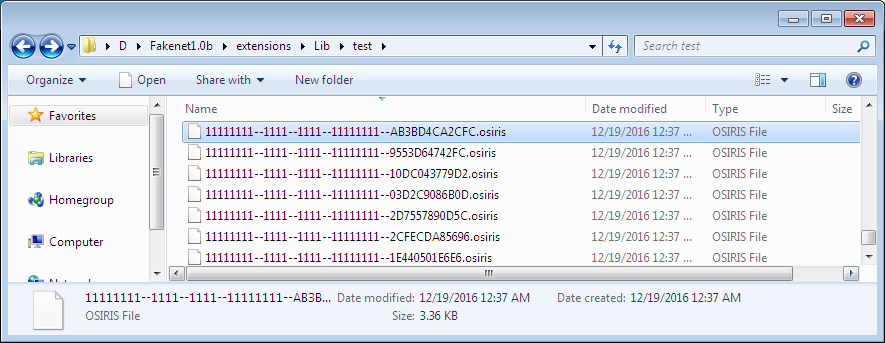
According to a test performed by Bleeping Computer’s Lawrence Abrams, under the hood RansomFree works by creating randomly-named folders throughout the filesystem that act as honeypots.
These folder names start with characters like ~ or ! because they are low on the ASCII table and thus will be scanned first by ransomware.
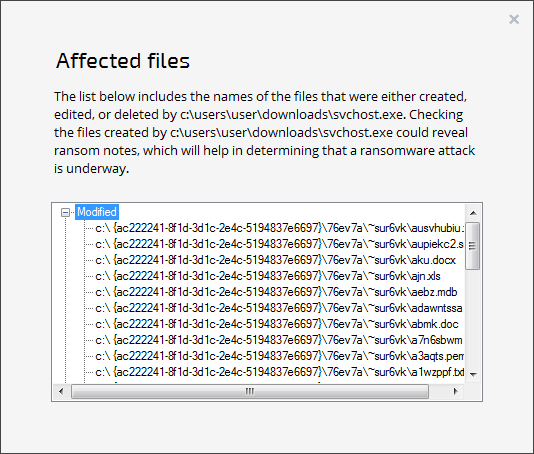
RansomFree monitors these files, and whenever they change, it detects the originating process and pauses it.
At this stage, RansomFree also shows a prompt, asking the user if he wants to stop the source process, or allow it to continue to execute.
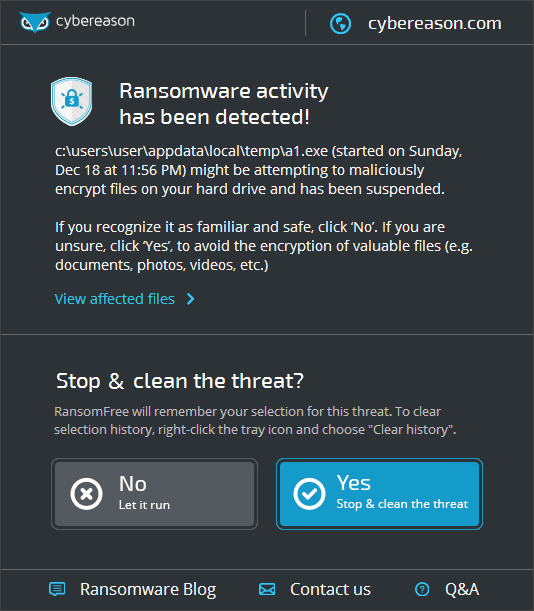
In a limited set of tests carried out by Bleeping Computer, RansomFree stopped the latest version of Locky (Osiris), Cerber, and Globe.
According to CyberReason, RansomFree also includes behavioral detections, but it is unsure if this is the same detection process that is described above. CyberReason has stated that it can handle more than 40 different ransomware strains, including Locky, Cryptowall, TeslaCrypt, Jigsaw, Cerber, and others.
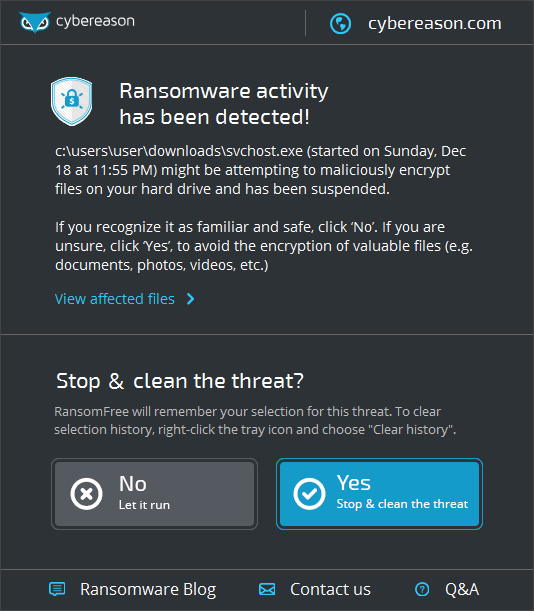
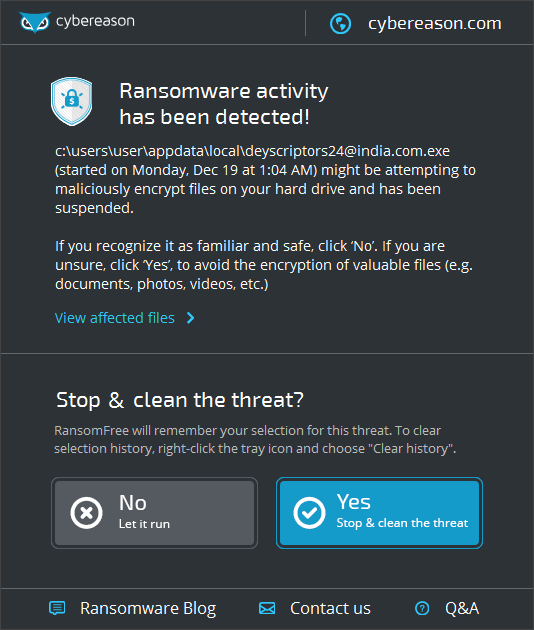
CyberReason says that RansomFree can detect when an abnormal encryption-heavy process starts (specific to ransomware families), on both the local computer and on shared and/or network drives.
The downside is that RansomFree needs a short amount of time to detect the start of the encryption operations. This means that a few of your files will be encrypted before RansomFree detects anything wrong.
Despite this, many users would happily sacrifice a few files if they can save the rest. However, the best course of staying safe from ransomware is to complement RansomFree with a solid computer backup policy.
RansomFree falls in the same category of anti-ransomware tools (called vaccines) as Malwarebytes’ Anti-Ransomware (formerly Nathan Scott’s CryptoMonitor), Bitdefender’s Anti-Ransomware Tool, Kaspersky Labs’ Anti-Ransomware Tool for Business, and Sean Williams’ Cryptostalker (for Linux only).
Below is a demo video of RansomFree in action, provided by Cybereason.
https://youtu.be/nr1w2mrOpto
Source:https://www.bleepingcomputer.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











