2016 is almost over and it definitely taught us one thing; Ransomware is here to stay and it’s only going to get worse. With even the smaller ransomware developers earning a lot of money, the ransomware explosion is going to continue with more innovative techniques used in 2017.
Therefore, it is important that every computer user, whether you are only using a computer at home or in the enterprise, needs to understand how to harden and protect their computer from ransomware. To help you, I have put together the most important steps a computer user needs to do in order to not only protect themselves from ransomware, but other malware that use similar infection methods.
I know this article is long, but computer security is something that takes effort. If you want to protect your computer and your assets, then I strongly suggest you print this article and read it as time permits.
Make sure you are doing backups!
Backup, Backup, BACKUP! This absolutely the most important task that needs to done to protect their data from being encrypted. The reality is that if you have up-to-date backups, ransomware becomes more of a nuisance than a threat. This is because you can simply remove the infection and then restore your data from backups.
Unfortunately, simply adding an extra hard drive to a computer and backing up to it once in a while is not enough. This is because ransomware will target and encrypt all the drives on a computer, including mapped network drives, and sometimes even target unmapped network shares. This means that backups on local and network storage could be encrypted as well.
Therefore, I strongly suggest that users invest in a good cloud backup strategy. Since most cloud backups do not map to a computer as a drive letter, the backups are safe from being encrypted and can easily be used to restore files.
If you do not wish to use a cloud backup, but want to rely on local storage, then make sure to either disconnect the storage devices after backups or make the backup computer isolated and inaccessible over file sharing. The only problem with a backup strategy using local storage is if that computer becomes infected, the backups are gone as well.
Install a antivirus or antimalware solution that has ransomware behavior detections.
Make sure you have a reliable anti-virus or anti-malware solution installed on the computer. Cybercrime is only increasing and every computer needs good protection on it. I also suggest that you use a product that contains good behavioral detection in order to detect when ransomware infection, even brand new ones, are trying to encrypt your data and then stop it.
Always install Windows updates
On Patch Tuesday, the second Tuesday of every month, Microsoft releases updates for Windows. Many of these updates are security updates that protect your computer from vulnerabilities that could literally allow an attacker to execute whatever command they want on your computer.
As many ransomware infections are installed via scripts called exploit kits that target Windows vulnerabilities, if you receive a prompt from Windows that updates are ready to install, then you should immediately install them.
Keep programs on your computer updated
Just like Windows vulnerabilities, exploit kits also target vulnerabilities in commonly installed programs on your computer such as Java, Adobe Flash Player, Adobe Reader, and others. Therefore it is imperative that you keep these programs updated as well.
An easy to use program that can scan a computer for outdated programs is Flexera Personal Software Inspector. This program will monitor your installed apps and alert you when updates are available.
Make sure your SPAM filters are working
One of the largest distribution methods for ransomware is through SPAM emails that pretend to be shipping notices, resumes, bills, or tickets from government agencies. If you are using a web mail vendor like Gmail, Outlook, or Yahoo, then many of these types of SPAM emails will be filtered out for you.
Unfortunately, if you are not using a service that has good SPAM filtering, then these types of emails may sneak through.
Enable the viewing of Extensions
By default, Windows does not show the extensions of a file when you are viewing a folder. This makes it easy for malware distributors to trick a user into thinking a executable file is actually a more familiar Word, Excel, or a PDF document A victim will open this file expecting it to contain data, but in reality they just ran a program that installs the malware. You can see an example of a program disguised as a PDF below with the showing of extensions enabled and disabled.
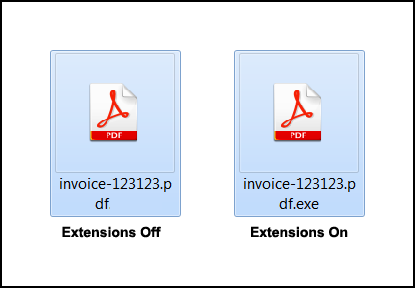
I suggest that everyone immediately enable the viewing of file extensions to make it harder for malware developers to trick you into launching their programs. To learn how to enable extensions, you can follow the steps in this tutorial: How to show File Extensions in Windows
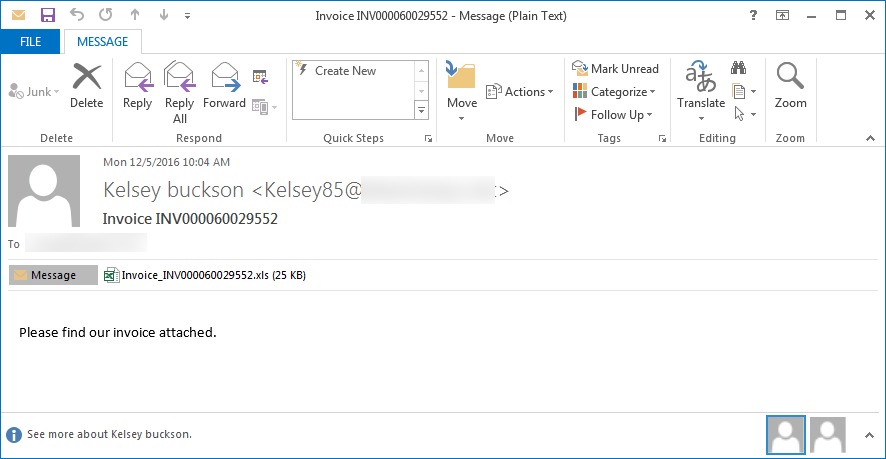
Do not open attachments without confirming that someone actually sent it to you
When ransomware is distributed via SPAM, in many cases the downloader or actual infection is attached as an attachment. If you receive an attachment and are unsure why it was sent or who it may have come from, do not open it without first confirming with the person that they actually sent it or by scanning it with VirusTotal. An example ransomware attachment can be seen below.
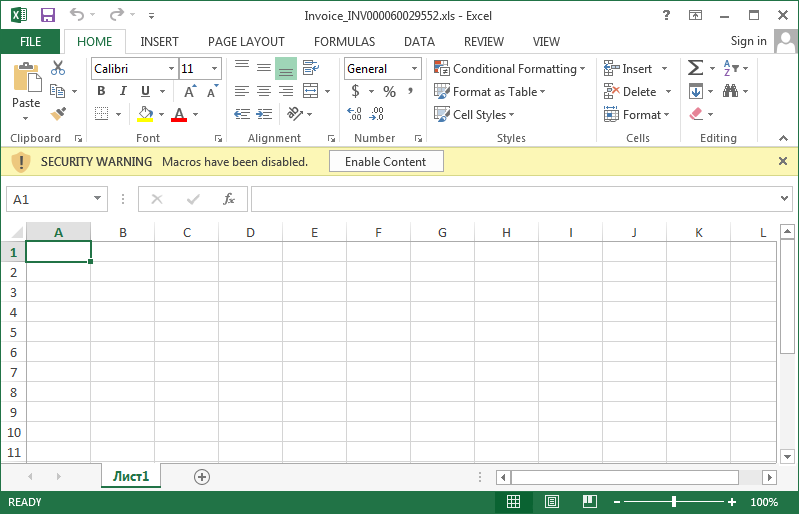
If you do make the mistake of opening an unknown attachment and see a message that you should click a button to enable macros or enable content, as shown below, DO NOT DO IT as this will just download and install the ransomware.
Be careful of what you download from the Internet
Free downloads from the Internet may also come with a hidden ransomware surprise. If they weren’t criminal enough already, it has been discovered that some adware bundles are now bundling ransomware. When downloading programs it is important that you only download from sites that you trust and always read the license agreements.
Rename vssadmin
Shadow Volume Copies are used by Windows to automatically store backups, or previous versions, of files on a computer. These backups can then be used to restore data that was changed or deleted.
Ransomware devs know about this too, so many ransomware infections will execute the vssadmin.exe command in order to delete all shadow volume copies on a computer so that they cannot be used to restore encrypted files.
Unless you have software that relies on vssadmin, I strongly suggest you read this article on how to rename it without losing functionality: Why Everyone Should disable VSSAdmin.exe Now!
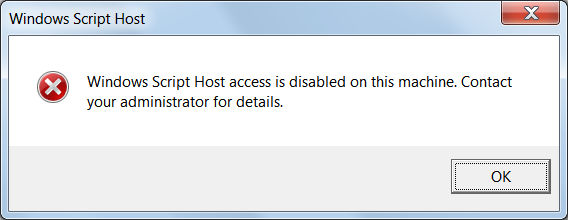
Disable Windows Script Host
Many ransomware infections are installed via attachments that are script files coded in Jscript or VBS. Unless you are normally executing Jscript or VBS files, and you would know if you are, then I suggest that you disable the ability to launch these types of scripts in Windows.
This article from Microsoft explains how to disable the Windows Script Host: Disabling Windows Script Host. Once the scripting host is disabled, if a script is launched you will see a message like the following.
Disable Windows PowerShell
Just like Windows scripting, the Windows PowerShell is also used to install ransomware or even encrypt files. If you are not using PowerShell on your computer, you can disable the execution of PowerShell (ps1) scripts from running by entering this command in a Windows Elevated Command Prompt.
powershell Set-ExecutionPolicy -ExecutionPolicy RestrictedIf it was set properly, when you execute a PowerShell script, you will see a message stating that PowerShell scripts have been disabled.
Note: As PowerShell becomes more and more popular, disabling the execution of PowerShell scripts could cause possible issues with legitimate programs. If you find that the execution of PowerShell scripts is necessary, you can change the Set-ExecutionPolicy to another level as described here.
Use strong passwords
Make sure you use strong passwords to protect your computer from unauthorized access. The goal is to make it hard for attackers, so do not use an easy password like 12345 and instead use a hard one like 1$!2M849dy1%.
This is because there are some ransomware infections that are installed by attackers logging into Remote Desktop connections that are secured with weak passwords, which leads us to my next suggestion…
If you do not need Remote Desktop, disable it, otherwise change the port!
If you are not using Remote Desktop, then there is absolutely no reason to keep it enabled.
If you are using it, then you should change the port to something other then the default port of 3389. To learn how to change the port used by Remote Desktop, you can read this tutorial: How to change the Terminal Services or Remote Desktop Port
As most attackers use scripts or scanners to search for open Remote Desktop computers on the default TCP port of 3389, by changing the port you have made your computer invisible to these tools.
Setup Software Restriction Policies
Software Restriction Policies is a method that allows you to create various policies that restrict what folders an executable can be started from. For more information on how to manually setup Software Restriction Policies, you can see this part of the Locky Guide.
For those who want to let a program do all the work for them, you can use the free CryptoPrevent program, which sets the policies for you. There is a premium version that offers a few extra benefits. In full disclosure, BleepingComputer is an affiliate of FoolishIT and earns a commission from the sale of their premium versions.
Create a Application White List Policy
This last one is not for the faint of heart and can take quite a bit of tweaking to get it to work. A Software White List Policy is when you configure Windows to only allow programs to execute that you specify. This prevent any unknown programs from running and essentially locks your computer down completely from allowing an unauthorized program to run.
The problem, though, is that this can take quite a bit of work to get setup properly. For those who want to give it a try, we have a White List guide here: How to create an Application Whitelist Policy in Windows
Conclusion
Though it may feel like there are a lot of steps, most of them require you to just change your computing habits or perform a task once and not worry about it again. If you follow these steps, not only will you be protected from ransomware, but you will also be protected from almost all other malware.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











