Router manufacturers such as Netgear and ZyXEL have failed to address seven security flaws reported by security researchers in the last three or more months.
Following unofficial industry standards, the security teams who found these flaws published their findings, so users can take precautionary measures, and decide if they still want to keep using the vulnerable devices, or replace them with more secure equipment.
Three vulnerabilities affecting Netgear routers
The first issues that came to light were discovered by Pedro Ribeiro, an independent security researcher.
Ribeiro found three bugs affecting Netgear WNR2000 routers. One of these flaws was a remote code execution (RCE) issue that allows an attacker to take the router under his control without providing proper authentication credentials. Another flaw allowed an unauthenticated attacker to recover the router’s admin account password.
The researcher says he confirmed these three flaws in Netgear WNR2000 v5 routers, but theoretically, these flaws also affect v4 and v3 versions of this particular router model.
The good news is that this RCE flaw is exploitable only if the remote administration feature is enabled on the router. The bad news is that for v4 and v3 router models, this is turned on by default, while in v5, a user must enable it manually.
Using Shodan, a search engine for Internet-connected devices, Ribeiro says he found over 10,000 vulnerable routers connected online, with their remote administration panel turned on.
“There are likely tens of thousands of vulnerable routers in private LANs as this device is extremely popular,” Ribeiro explained. A determined attacker could find ways to exploit this vulnerability on private LANs if he wished to.
This is not the first security issue that came to light this month that affected Netgear routers this month. Earlier in December, the United States Computer Emergency Readiness Team (US-CERT) published a security alert warning users to stop using Netgear R6400 and R7000 models because of an unpatched security flaw.
Vulnerabilities in ZyXEL routers
Today, security firm SecuriTeam also published a report on four security flaws affecting three router models manufactured by ZyXEL, a white-label router vendor.
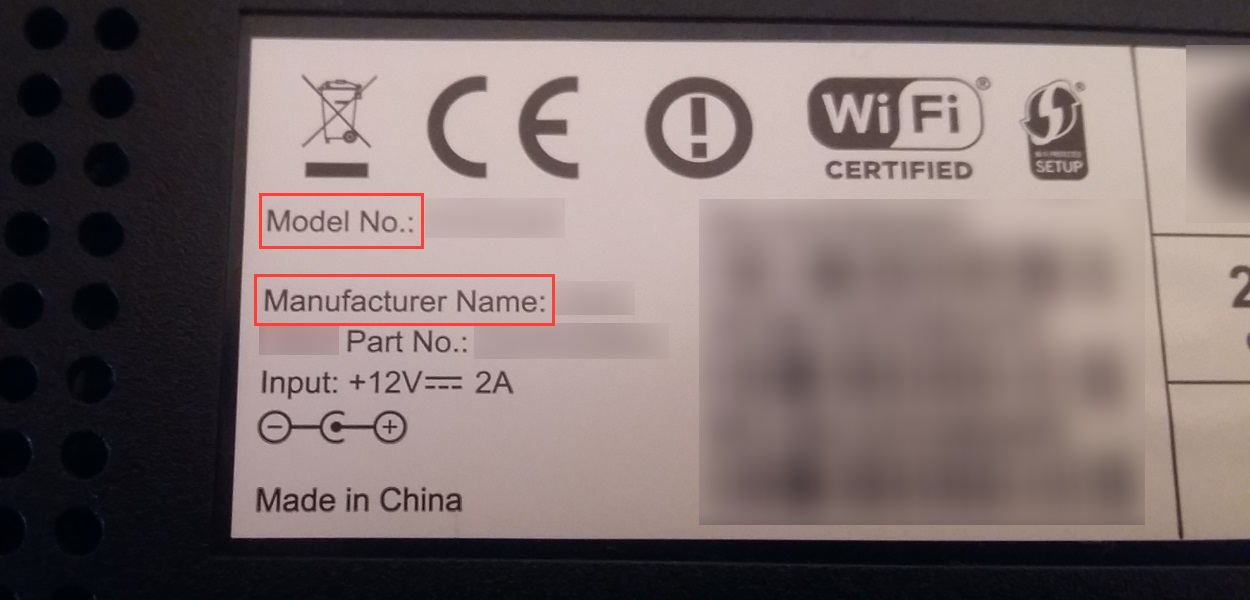
ZyXEL provides these routers to ISPs around the world, which most of the times use their own logo and branding on the top box. Users might need to check the label on the bottom of their device to see who manufactured the router and check out its model number.
The three router models and vulnerabilities are P660HN-T v1, P660HN-T v2, and Billion 5200W-T. The four vulnerabilities are:
- Unauthenticated remote command execution vulnerability – P660HN-T v1 router
- Unauthenticated remote command execution vulnerability – Billion 5200W-T
- Authenticated remote command execution vulnerability – Billion 5200W-T
- Unauthenticated remote command execution vulnerability – P660HN-T v2
According to SecuriTeam, these flaws allow an attacker to take control of affected products by issuing maliciously-crafted HTTP requests.
Furthermore, the routers also come with simplistic username and password combinations that are easy to guess. Proof of concept code has been released by SecuriTeam. Ribeiro also released proof-of-concept code for his Netgear flaws.
Vendor response
Probably the most disheartening part of these security flaws is the vendor response the research teams received for their reports. Which was none. We quote Ribeiro and SecuriTeam’s disclosure timelines:
26.09.2016: Email sent to NETGEAR (security () netgear com) asking for PGP key, no response.
28.10.2016: Email sent to NETGEAR (security () netgear com) asking for PGP key, no response.
26.11.2016: Disclosed vulnerability to CERT through their web portal.
29.11.2016: Received reply from CERT. They indicated that NETGEAR does not cooperate with them, so they recommended getting CVE numbers from MITRE and releasing the vulnerability information. Email to MITRE requesting CVE numbers, no response. Email sent to NETGEAR (security () netgear com) asking for PGP key, no response.
20.12.2016: Public disclosure.

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











