Microsoft recently patched a critical vulnerability in its ubiquitous built-in antivirus engine. The vulnerability could have allowed attackers to execute malicious code by luring users to a booby-trapped website or attaching a booby-trapped file to an e-mail or instant message.
A targeted user who had real-time protection turned on wasn’t required to click on the booby-trapped file or take any other action other than visit the malicious website or receive the malicious e-mail or instant message. Even when real-time protection was off, malicious files would be executed shortly after a scheduled scan started. The ease was the result of the vulnerable x86 emulator not being protected by a security sandbox and being remotely accessible to attackers by design. That’s according to Tavis Ormandy, the Google Project Zero researcher who discovered the vulnerability and explained it in a report published Friday.
Ormandy said he identified the flaw almost immediately after developing a fuzzer for the Windows Defender component. Fuzzing is a software testing technique that locates bugs by subjecting application code to corrupted data and other types of malformed or otherwise unexpected input.
“I took a quick stab at writing a fuzzer and immediately found heap corruption in the ERNEL32.DLL!VFS_Write API,” he wrote on June 7. “I suspect this has never been fuzzed before.” Google published the report on Friday after Microsoft released an update that patched the code-execution flaw. It was the third critical Windows Defender vulnerability Project Zero researchers have uncovered in the past seven weeks. The emulator is used to execute untrusted files that might have the potential to execute code. Asked if Microsoft hadreviously fuzzed the Windows Defender component, a company representative said yes.
“Fuzzing is one of a number of techniques we employ to update and strengthen our software,” the representative said in an e-mail. “It is a standard practice we use as part of the Security Development Lifecyle for our products.”
In an advisory that was also published Friday, Microsoft officials said attackers who exploited the vulnerability could execute arbitrary code that would run with the rights of a LocalSystem account. According to this document, the account has “extensive privileges on the local computer and acts as the computer on the network.” Exploiting the memory corruption bug in the Windows Defender emulator, an attacker could take control of the system and perform a variety of tasks, including installing programs, viewing, changing, or deleting data, as well as creating new accounts with full user rights.
Warning, this file may crash your server
As a testament to the ease of triggering the bug, Ormandy took special precautions in publishing some of the proof-of-concept exploits, which were linked to a file named testcase.txt. “Note that, as soon as the testcase.txt file touches disk, it will immediately crash the MsMpEng service on Windows, which may destabilize your system,” he wrote. “The testcases have been encrypted to prevent crashing your exchange server.”
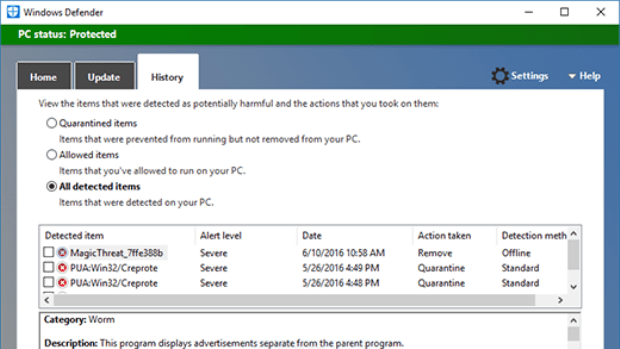
In early May, Microsoft patched a separate severe code-execution vulnerability in the malware protection engine. That’s the engine that powers Windows Defender, which is installed by Default on all consumer PCs running supported versions of Windows. Ormandy called the flaw “the worst Windows remote code exec in recent memory,” and he warned that attacks “work against a default install, don’t need to be on the same LAN, and [they’re] wormable.”
Ormandy and fellow Project Zero researcher Natalie Silvanovich discovered the issue and reported it. On May 25, Microsoft closed yet another code-execution hole in the malware projection engine that, like the other two, could be exploited with little or no interaction on the part of targets.
The steady accumulation of critical AV vulnerabilities unearthed by Ormandy has involved products from a variety of companies, including Kaspersky Lab, Trend Micro, Symantec, McAfee, Eset, and Comodo. Taken together, the findings demonstrate how AV use can open users to attack they otherwise wouldn’t be vulnerable to. At the same time, AV in many cases prevents infections that would otherwise prove costly, particularly for less experienced users who aren’t likely to be individually targeted by state-sponsored hackers.
Source:https://arstechnica.com/security/2017/06/latest-high-severity-flaw-in-windows-defender-highlights-the-dark-side-of-av/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.