In a tech application that looks like something out of a sci-fi movie, the Federal Bureau of Investigation (FBI) resorted to a court order to gain access to all Android devices located near the Seattle police union building on the afternoon of August 24, 2020, when representatives of the Black Lives Matter (BLM) social movement tried to start a fire in the building, forcing the evacuation of all personnel.
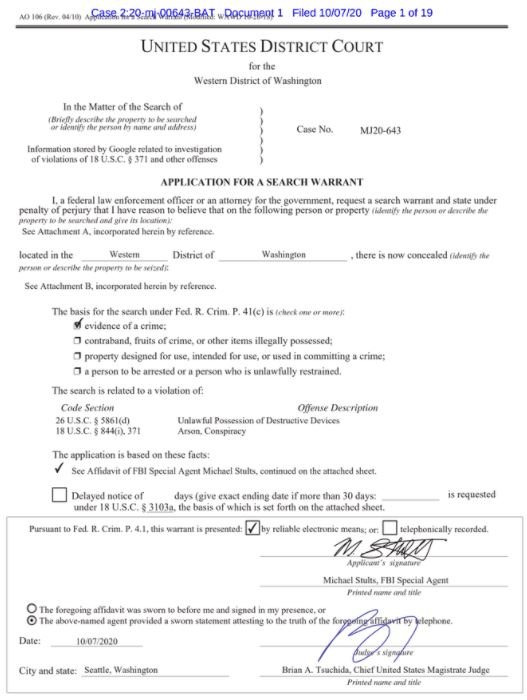
According to the report, the investigative agency resorted to the so-called “geofence warrant” to force Google to hand over information about devices using its popular mobile operating system, located in the area at the time of the attack.
During the investigation of the incident, an officer stated that it all began at almost midnight, when two unidentified suspects caused intentional damage to the building using homemade explosives: “Based on this information, we believe there is probable cause to seek information in Google’s possession and related to devices located near the scene of the incident.”

In the order, Google is required to hand over location history data, including GPS data and information related to visible WiFi points and Bluetooth packets transmitted from these devices to Google, determining the devices within reach of the investigation using the coordinates, date and times provided by the FBI.
For obvious reasons, privacy activists expressed concern, believing that Google should not be able to hand over these confidential records to law enforcement without a clear case and as an attempt to locate potential suspects.
These kinds of measures can cause anyone located around a crime scene to be considered a suspect; if your mobile device shows any indication of this, the authorities can send you a subpoena and even request full access to the information stored on your smartphone.
A Google spokesperson said, “As with any other legal request, we have a rigorous process that is designed to protect the privacy of our users while supporting the important work of law enforcement,” though it has not been confirmed whether the FBI will have access to the desired information.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











