Security researchers from Kaspersky Lab discovered a weakness in Microsoft Windows that can allow an attacker to take full control of a computer in just a few minutes. This highest level of control is called SYSTEM access, which basically means the attacker can do anything on the machine, install programs, read data, change settings, or even hide their presence completely. Surprisingly, even after being informed, Microsoft did not treat this issue as highly dangerous and has not rushed to fix it.
To understand this issue, think of Windows as a large office where different employees (programs and services) constantly communicate with each other to get work done. This communication happens through something called Remote Procedure Call(RPC). RPC allows one program to request another program to perform a task, even if they are running separately. This system is very powerful but also quite complex, and over the years it has often been a source of security problems.
The vulnerability lies in how this communication system is designed. Normally, when one service wants to talk to another, it sends a request. If the requested service is not running, the system still tries to connect and eventually fails. However, during this failure moment, an attacker can step in and trick the system. They can create a fake service that looks exactly like the real one and intercept the request. This is like pretending to be someone else in the office and answering calls meant for them.
Now comes the critical part. Windows has a feature where a service can temporarily act as another user. This is known as impersonation. If a high level service (like one running with SYSTEM or administrator rights) connects to the attacker’s fake service, the attacker can inherit those same powerful permissions. In simple words, the attacker tricks the system into handing over its master key.
One example involves something called the Group Policy Service. This service manages important system settings. When it tries to update these settings, it may attempt to contact another service, such as the Remote Desktop Service. If that service is turned off, the attacker can jump in and pretend to be it. When the Group Policy Service connects, the attacker’s fake service captures the request and gains SYSTEM level access. What started as a low-level access (like a basic network service account) suddenly becomes full system control.
What makes this attack even more concerning is that it doesn’t always require active effort from the attacker. Sometimes, it can happen automatically. For example, when a user opens a browser like Microsoft Edge, it may trigger background communication between services. If an administrator opens the browser, the attacker can take advantage of that moment to gain high level access. In other cases, some system services regularly try to connect to other services in the background. An attacker can simply wait, and within a few minutes, the system may unknowingly give them the access they want.
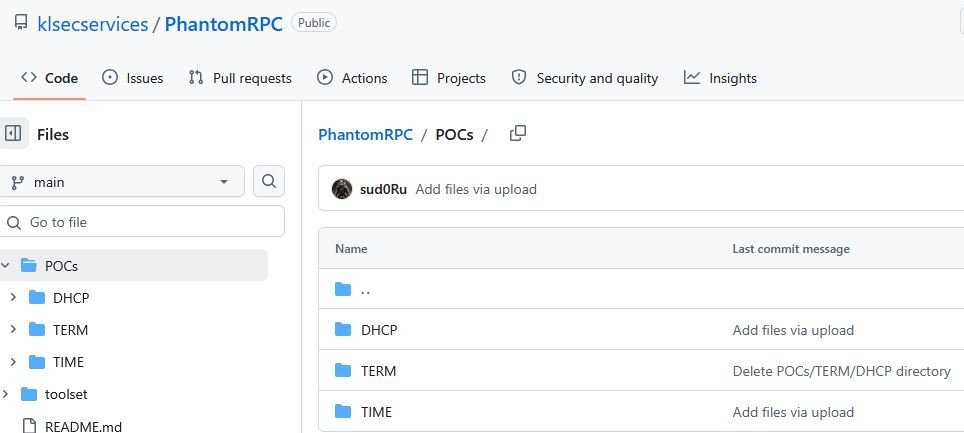
Another example involves the DHCP Client, which helps a computer get an IP address from the network. If this service is disabled and replaced with a fake version, even a simple command like ipconfig can trigger the attack. When an administrator runs this command, their high-level privileges can be passed to the attacker. A similar trick works with the Windows Time Service, which tries to sync time but can be fooled if its expected communication channel is missing. Proof of concept can be found at github.
The root of the problem is deeper than just a few services. Windows does not properly verify whether the service it is connecting to is genuine or fake. This means any program can pretend to be a trusted service if it uses the correct name and interface. Since RPC is used widely across the system, there are many possible points where this attack could happen. It’s like having many unlocked doors in a building any one of them could be used to break in.
To identify these weak points, researchers studied system logs and looked for failed RPC connection attempts. These failures are important because they show where the system tried to connect to a service that wasn’t available. If such a request comes from a highly privileged process, it becomes a potential attack opportunity. Each of these failed connections is like a door left slightly open for attackers.
Fixing this issue completely is not easy. The problem is built into how the system is designed, so it would require major changes to the Windows architecture. For now, only partial solutions are available. For example, administrators can reduce risk by making sure important services are always running, so there are no “empty” connection points. They can also limit which processes are allowed to impersonate other users.
This vulnerability has been tested on modern systems like Windows Server 2022 and Windows Server 2025 with the latest updates, and it still works. Based on how Windows is built, it likely affects many other versions as well. That means a large number of systems could potentially be at risk.
In summary, this is a serious design flaw that allows attackers to quietly take over a system by exploiting normal communication between services. The attack is simple, does not always require user interaction, and can happen quickly. While there are ways to reduce the risk, a complete fix will require deeper changes from Microsoft. Until then, organizations need to stay alert and take preventive measures to protect their systems.

Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator. He is a cyber-security researcher with over 25 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked with Google and Citrix in development of cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.











