Update your iOS: Vulnerability in Apple TouchID allows hacking iCloud accounts
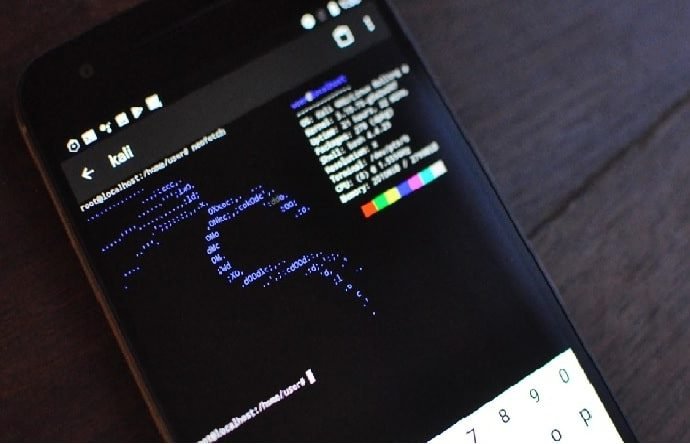
Security has become the main focus of marketing campaigns for Apple devices, although we should not forget that any product is completely safe from some threats, as mentioned by iOSRead More →