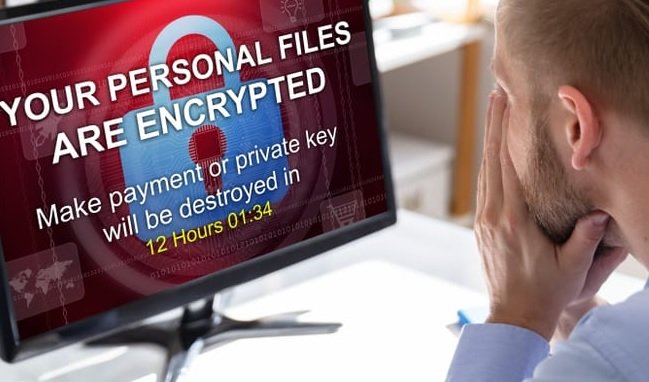
Session hijacking & malware injection vulnerabilities found in Apple Mail app and AirShare affecting iPhone, iPad & Mac
A new report has revealed new cybersecurity threats. According to vulnerability assessment experts, ZecOps says multiple iPhone models are exposed to exploiting an Apple Mail-related vulnerability. Apparently, exploiting this securityRead More →