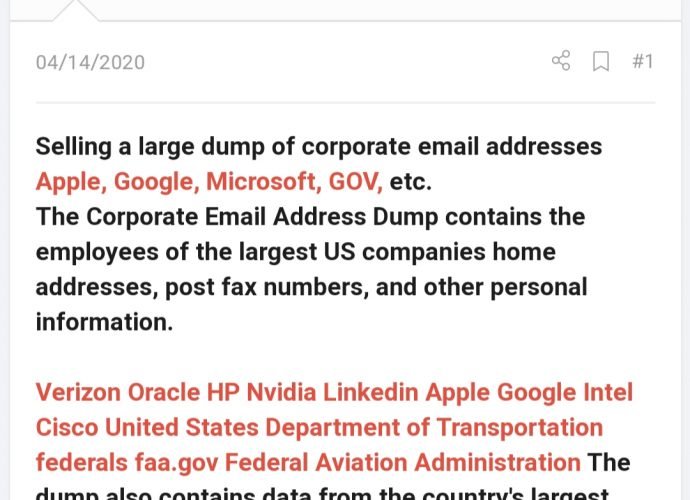
Critical vulnerabilities in Adobe Bridge, Magento and Illustrator allow remote hackers spy on you
Adobe’s penetration testing services experts have released multiple security updates for Adobe Illustrator, Bridge, and Magento products, which will be fixed multiple vulnerabilities, including some that would allow threat actorsRead More →