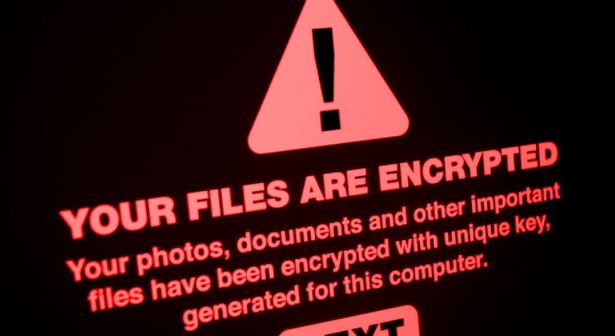
FBI issues alert on increasing attacks of Conti ransomware. Multiple 911 call centers infected by ransomware
In its most recent security alert, the Federal Bureau of Investigation (FBI) unveiled the detection of a wave of Conti ransomware attacks targeting first aid and health care networks inRead More →