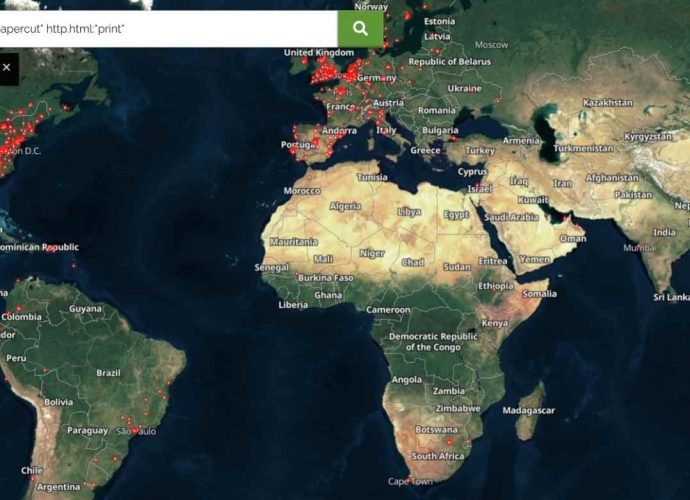
New way to hack millions of users using Papercut printer software
Researchers from VulnCheck have created a new attack for the previously discovered serious issue in PaperCut servers. This exploit, which is tagged as CVE-2023-27350 and has a CVSS score ofRead More →