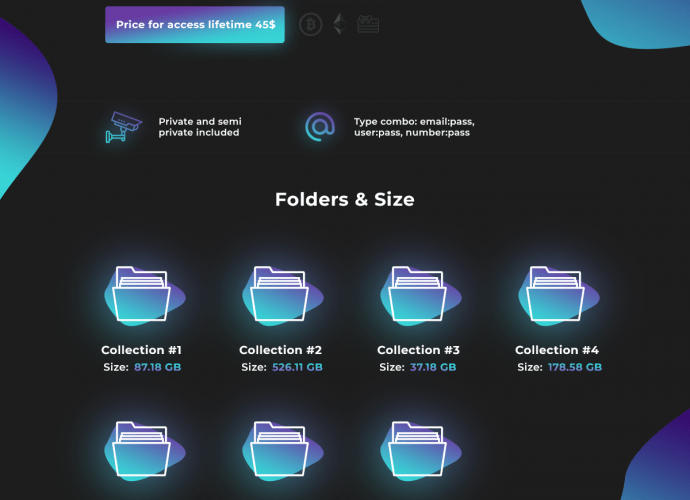
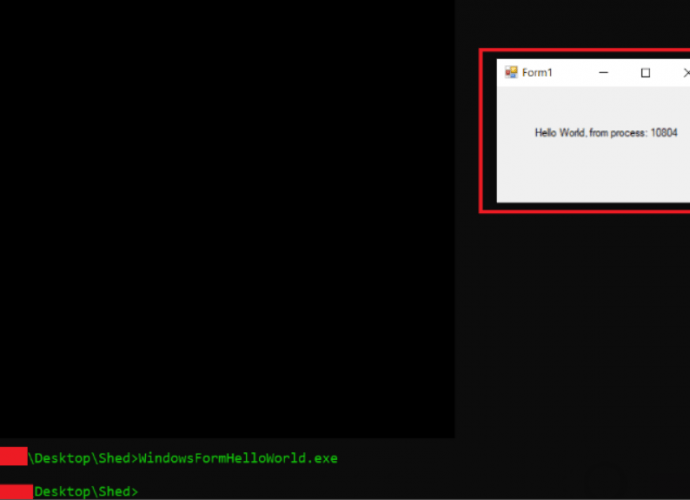
ATTENTION: Torrents downloaded from The Pirate Bay contain a dangerous malware
Malicious hackers have infected some torrents on this platform with a malware functional in Windows operating systems Although in general this practice does not generate major drawbacks, experts in networkRead More →