How to crash any user’s WhatsApp account with a dangerous message
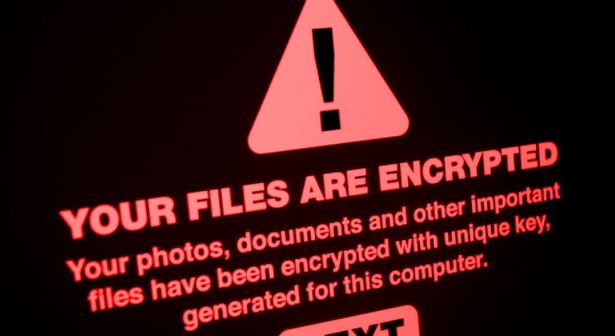
The world’s most widely used software tools are often the subject of malicious attacks and even small “hacks” that cause service failures. Application security experts detail the detection of aRead More →