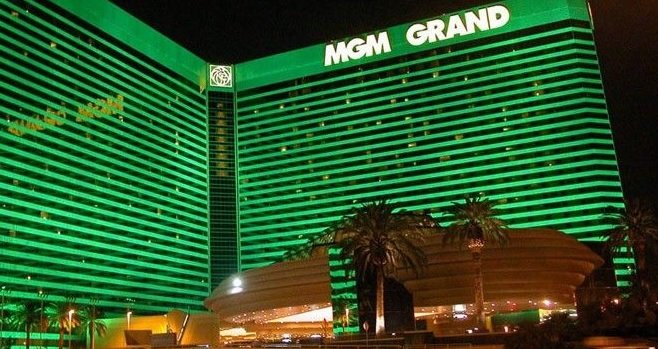
Las Vegas MGM was hacked; details of over 10 million guests exposed online
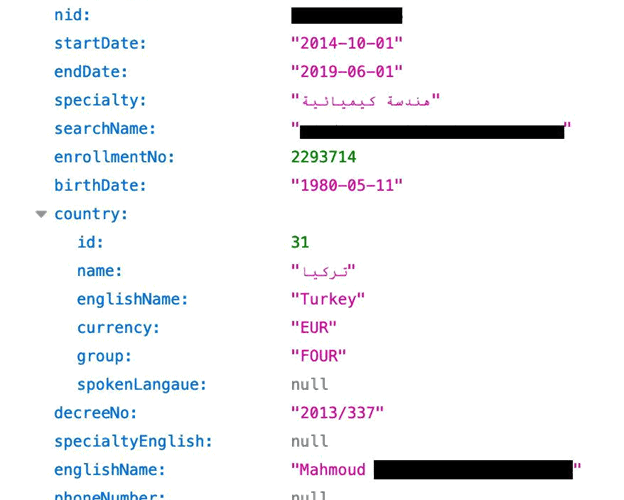
A data breach has compromised the information of millions of people who have stayed at MGM Resorts hotels, including Las Vegas’ MGM Grand. According to an information security firm, theRead More →