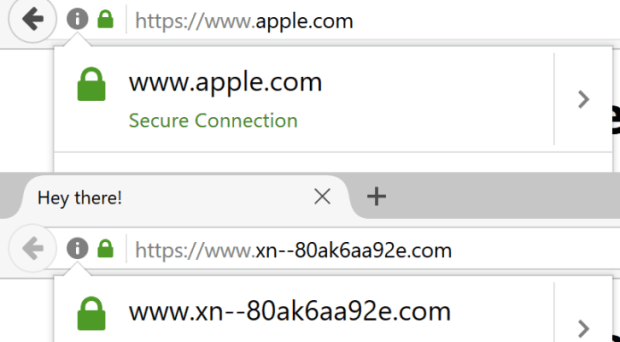
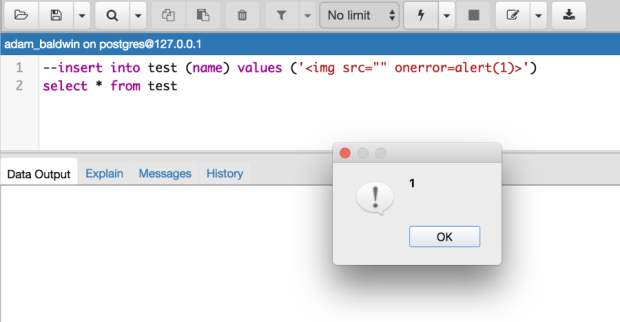
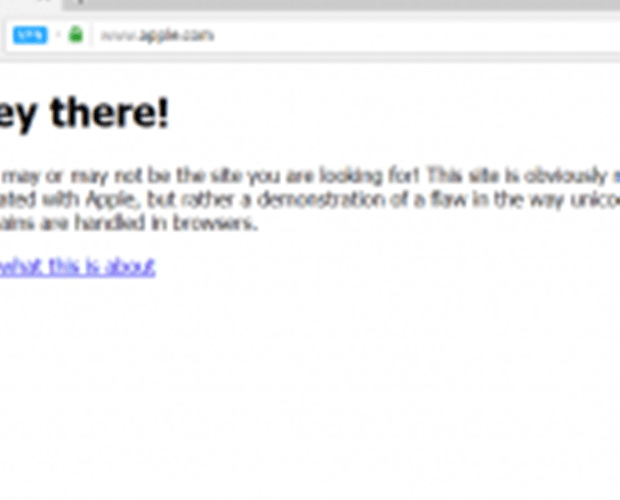
Homograph Phishing Attacks are almost impossible to detect on major browsers
The Chinese security Xudong Zheng is warning of Homograph Phishing Attacks are “almost impossible to detect” also to experts. The Chinese security researcher Xudong Zheng has devised a phishing techniqueRead More →