Point-of-Sale Malware Steals Driver’s License Information
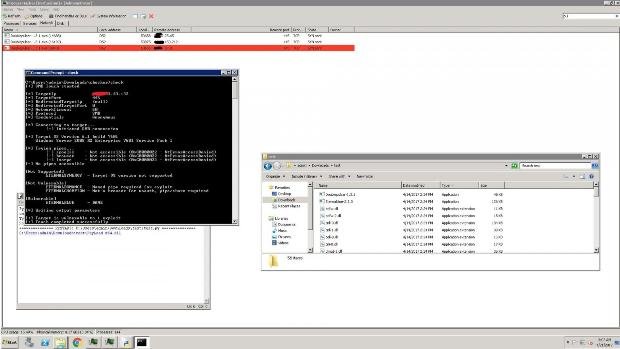
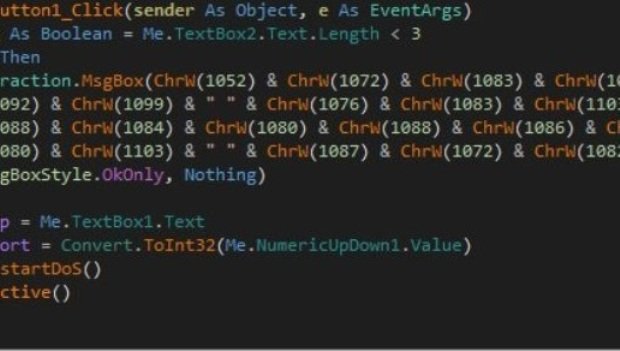
Malware specialized in infecting Point of Sale (PoS) software has gained the ability to search and steal driver’s license information, according to a report published by US cyber-security firm TrendRead More →