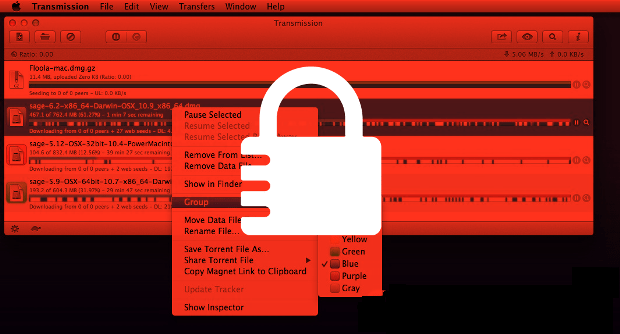
Burrp compromised to serve Angler EK and deliver TeslaCrypt ransomware
An Indian restaurant recommendation site contains injected code which redirects users to the Angler EK, which in turn drops TeslaCrypt (Trojan.Cryptolocker.N) on the computer. A popular Indian restaurant recommendation siteRead More →