HTTP GZIP Leaks Data on the General Location of Tor Websites
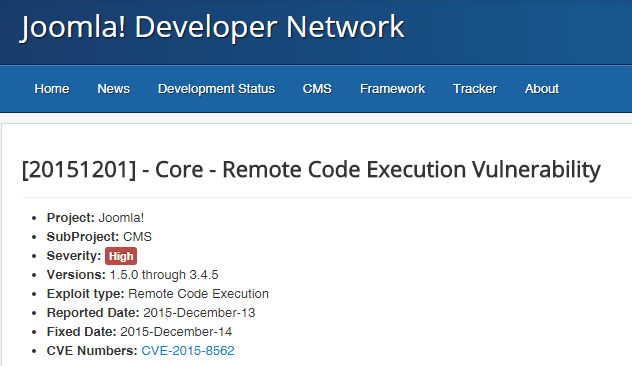
Some Tor servers may leak timezone info via gzipped files. Jose Carlos Norte, developer for the eyeOS virtual desktop project, has discovered an obscure setting in the HTTP GZIP compression formatRead More →