Authorities shut down Luminosity RAT used by buyers in 78 countries
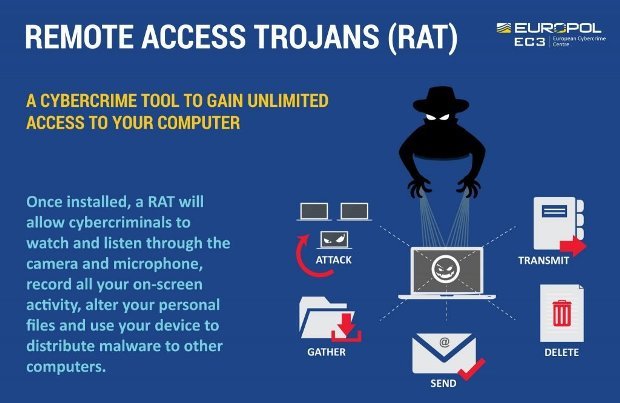
The popular Luminosity RAT has been shut down by authorities and its users have no access to it anymore. In a joint operation, the law enforcement authorities from Australia, Europe, andRead More →