Several polish banks hacked, information stolen by unknown attackers
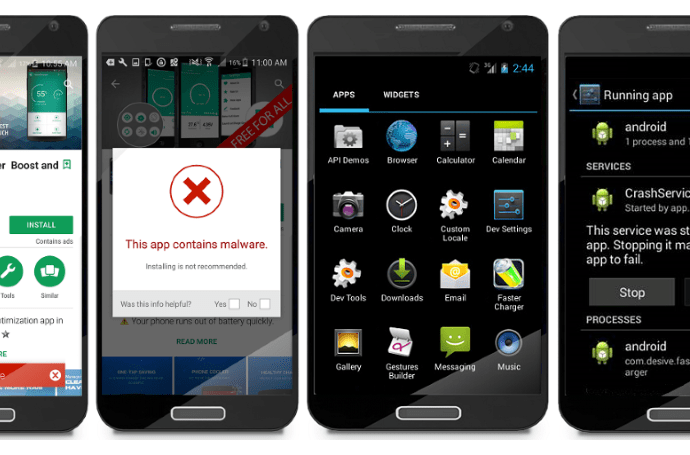
Polish banks are frantically scanning their workstations and servers while checking logs in the search of signs of infection after some of them noticed unusual network activity and unauthorised files on keyRead More →