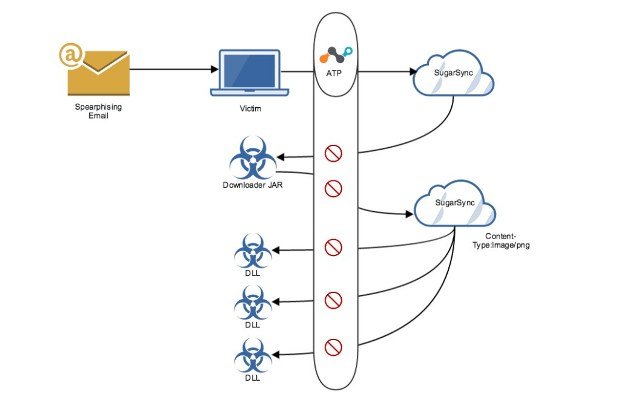
CloudFanta Malware Steals Banking Information Via Cloud Storage Apps
We recently published an overview blog about the CloudFanta malware campaign that uses the Sugarsync cloud storage app to deliver malware capable of stealing user credentials and monitoring online bankingRead More →