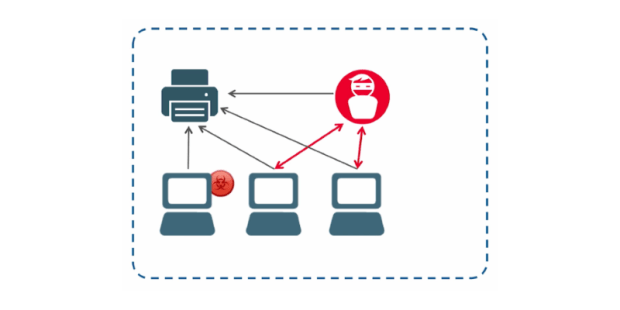
Vulnerability Exploitable via Printer Protocols Affects All Windows Versions
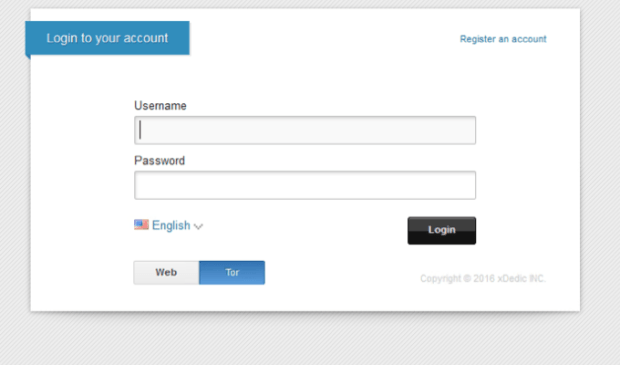
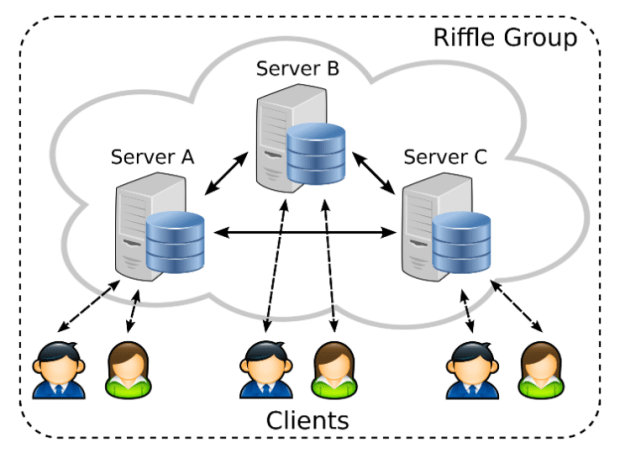
Introducing vulnerability of the year: CVE-2016-3238. Microsoft patched today a critical security vulnerability in the Print Spooler service that allows attackers to take over devices via a simple mechanism. The vulnerabilityRead More →