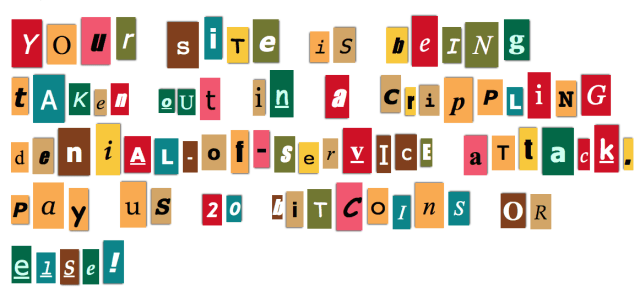
Pay or we’ll knock your site offline—DDoS-for-ransom attacks surge
One of the Internet’s oldest and crudest attacks experiences a resurgence. A number of sites have been hit by distributed denial-of-service attacks over the past week. Strong enough to knockRead More →