An attacker going by the name of Harak1r1 is hijacking unprotected MongoDB databases, stealing their content, and asking for a Bitcoin ransom to return the data.
These attacks have been happening for more than a week and have hit servers all over the world. The first one to notice the attacks was security researcher Victor Gevers, who, as part of Project 366 with the GDI Foundation, has been busy searching for unprotected MongoDB servers and alerting companies about their status.
Attacker asking for a ransom of 0.2 Bitcoin
On December 27, Gevers stumbled upon another MongoDB server that was left open to external connections and without a password on the admin account.
Unlike other instances he discovered in the past, this one was different. When he accessed the open server, instead of looking at the database’s content, a collection of tables, Gevers found only one table, named “WARNING”. The content of this table was:
{
"_id" : ObjectId("5859a0370b8e49f123fcc7da"),
"mail" : "harak1r1@sigaint.org",
"note" : "SEND 0.2 BTC TO THIS ADDRESS 13zaxGVjj9MNc2jyvDRhLyYpkCh323MsMq AND CONTACT THIS EMAIL WITH YOUR IP OF YOUR SERVER TO RECOVER YOUR DATABASE !"
}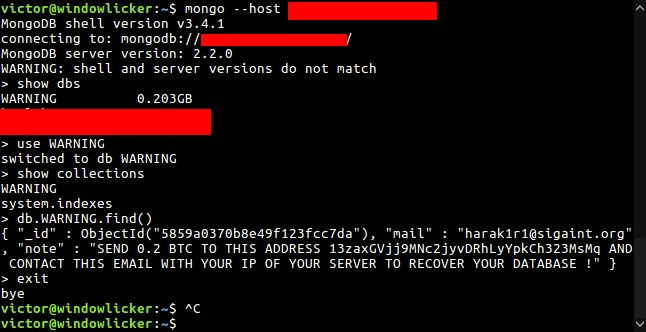
According to Gevers, the attacker had accessed the unprotected MongoDB database, exported its content, and replaced all data with the above table.
“I was able to confirm [this] because the log files show clearly that the date [at which] it was exported first and then the new database with tablename WARNING was created,” Gevers told Bleeping Computer. “Every action in the database servers was being logged.”
The good news is that after Gevers informed the company who owned the database server, they were able to recover their data, which was just backed up right before the intrusion.
Similar attacks reported in China in the past week
A quick Google search for the attacker’s email address and Bitcoin address reveals other userscomplaining about similar incidents.
All incidents appear to have taken place in the past week, hinting at a mass-scan operation carried out by Harak1r1, who then accessed these systems and held their data for ransom.
“This is not ransomware. Database does not get encrypted. It only gets replaced,” Gevers wanted to make clear. “This is someone who does [this] manually or with a simple Python script.”
Gevers, who also posted his findings on Twitter, said that he’s been receiving requests for help from companies that have been hit by Harak1r1’s attacks.
“After posting this tweet, I got a few requests for help from organizations who paid to get a backup of their database back and wanted to make sure they cannot get hacked again,” Gevers said.
The problem of unprotected MongoDB instances
“I’ve been busy for years tracking down runnable systems and reporting them via a responsible disclosure to the organizations they belong to,” Gevers added. “I’ve been doing this for a long time and I have over 5200 responsible disclosures made worldwide.”
The security expert says that to blame for these incidents are old MongoDB instances deployed via cloud hosting services.
“The most open and vulnerable MongoDBs can be found on the AWS platform because this is the most favorite place for organizations who want to work in a devops way,” Gevers said. “About 78% of all these hosts were running known vulnerable versions.”
These vulnerable MongoDB versions are older DB instances were a default configuration left the database open to external connections via the Internet.
MongoDB, Inc., the company behind MongoDB has fixed this issue a few months later, but companies keep using the outdated versions, in most cases, because those versions were the default MongoDB images on AWS and other cloud hosting services.
MongoDB admins that want to avoid having their database taken over should update to the latest MongoDB version and follow the company’s official security best practices.
11 victims paid the ransom
Webmasters should be very wary because this attack wave is no joke. According to statistics from Blockchain.info, at least eleven MongoDB owners have paid Harak1r1 the 0.2 Bitcoin ransom to recover their files.
This is not the first time crooks have targeted open database systems and held their data for ransom.
Source:https://www.bleepingcomputer.com

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











