A newly discovered malware family that preys on jailbroken iPhones has collected login credentials for more than 225,000 Apple accounts, making it one of the largest Apple account compromises to be caused by malware.
KeyRaider, as the malware family has been dubbed, is distributed through a third-party repository ofCydia, which markets itself as an alternative to Apple’s official App Store. Malicious code surreptitiously included with Cydia apps is creating problems for people in China and at least 17 other countries, including France, Russia, Japan, and the UK. Not only has it pilfered account data for 225,941 Apple accounts, it has also disabled some infected phones until users pay a ransom, and it has made unauthorized charges against some victims’ accounts.
Researchers with Palo Alto Networks worked with members of the Chinese iPhone community Weiphone after members found the unauthorized charges. In a blog post published Sunday, the Palo Alto Networks researchers wrote:
KeyRaider has successfully stolen over 225,000 valid Apple accounts and thousands of certificates, private keys, and purchasing receipts. The malware uploads stolen data to its command and control (C2) server, which itself contains vulnerabilities that expose user information.
The purpose of this attack was to make it possible for users of two iOS jailbreak tweaks to download applications from the official App Store and make in-app purchases without actually paying. Jailbreak tweaks are software packages that allow users to perform actions that aren’t typically possible on iOS.
These two tweaks will hijack app purchase requests, download stolen accounts or purchase receipts from the C2 server, then emulate the iTunes protocol to log in to Apple’s server and purchase apps or other items requested by users. The tweaks have been downloaded over 20,000 times, which suggests around 20,000 users are abusing the 225,000 stolen credentials.
Some victims have reported that their stolen Apple accounts show abnormal app purchasing history and others state that their phones have been held for ransom.
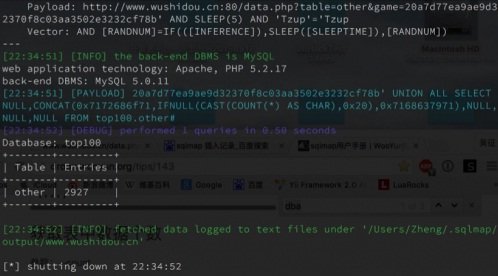
As if the theft of the Apple account credentials wasn’t bad enough, the data was uploaded to a website that contained a SQL-injection vulnerability. The flaw made it trivial for outsiders to access some of the records. Most of the e-mail addresses of affected uses suggest they are Chinese or possibly Chinese people living in other countries.
 The KeyRaider discovery provides a cautionary tale about the risks of jailbreaking iPhones. Most security experts discourage the practice unless it’s done by highly experienced people who know exactly what code they’re using to circumvent Apple engineers’ safeguards and, once that’s done, what alternative apps they’re installing.
The KeyRaider discovery provides a cautionary tale about the risks of jailbreaking iPhones. Most security experts discourage the practice unless it’s done by highly experienced people who know exactly what code they’re using to circumvent Apple engineers’ safeguards and, once that’s done, what alternative apps they’re installing.
Source:https://arstechnica.com/

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











