A decryptor has been released by ransomware expert BloodDolly that will allow victim’s encrypted by the ODCODC Ransomware to recover their files for free. Though the Command & Control servers are no longer active, many ransomware victims do not pay the ransom and hold on to their encrypted files in the hope that a decryptor can be created. These victims can now use BloodDolly’s decoder to recover their files.
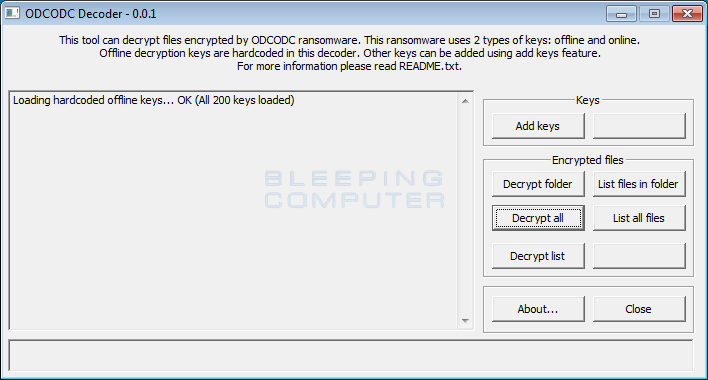
For those who were affected by the ODCODC ransomware, you can download the ODCODC Decoder from the following link: https://www.bleepingcomputer.com/forums/t/615172/odcodc-ransomware-odcodc-help-support-readthistxt/?p=4038795. Once downloaded, extract the zip file and read the readme.txt for instructions on how to continue.
As BloodDolly explains in his readme.txt instructions, ODCODC will attempt to download a unique key from the command & control server for each hard drive partition it encrypts. If it is unable to connect to the command & control server, it will instead randomly select one of 200 static encryption keys that can encrypt the victim while they are offline.
A victim can determine if they have a offline or online key by looking at the PCID specified in the readthis.txt ransom note. If the PCID contains an X, like JANKO-16098513X1781, then an offline key was used and the decoder can decrypt the files using the built-in keys.
On the other hand, if the PCID does not contain an X, like JANKO-L3710254317, BloodDolly can reconstruct the key using encrypted files. To reconstruct the key, BloodDolly will need either pair of encrypted and original file or any encrypted .doc, .xls or .ppt (not .docx, .xlsx, .pptx, etc) file. BloodDolly has included instructions on how to send him these files here.
Once the proper key has been determined, a user can simply run the ODCODC Decoder and decrypt their files. BloodDolly recommends that user’s backup the encrypted files before decrypting and to test the decryption on a few files before decrypting the whole drive.
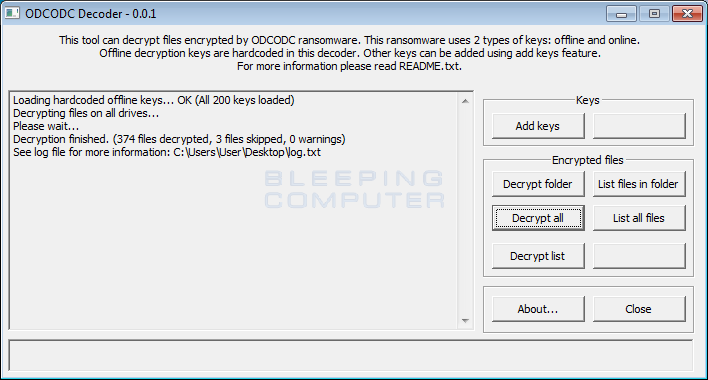
In my test, and others in the ODCODC Ransomware topic, ODCODC decoder has successfully been able to decrypt encrypted files. A big thanks to BloodDolly for releasing this tool!
Source:https://www.bleepingcomputer.com/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











