Deep Hosting — a Dark Web hosting service — admitted yesterday to suffering a major security incident during which “some sites have been exported.”
The hack took place on Saturday afternoon and was carried out by a hacker calling himself Dhostpwned, the name he used when he spoke with Bleeping Computer earlier today.
Hacker used PHP shell to take over hosting provider
According to a wiki page published by the Deep Hosting team, the hack took place after the hacker registered a shared hosting account on their service, and used it to upload two shells on their servers, one written in PHP and one in Perl.
A Deep Hosting investigation into the events that preceded the hack showed that the attacker was not able to execute the Perl shell, but the PHP version worked just fine.
“A large part of the PHP shell is unusable since a certain number of functions are blocked on the shared servers but one function was not blocked,” Deep Hosting wrote in a wiki page detailing the security incident. “The attacker was able to access the server and execute a commands [sic] with limited rights.”
According to a timeline of their investigation — embedded below — it took the Deep Hosting almost a full day to understand what really happened, detect the point of intrusion, and change FTP and SQL password for all user accounts.
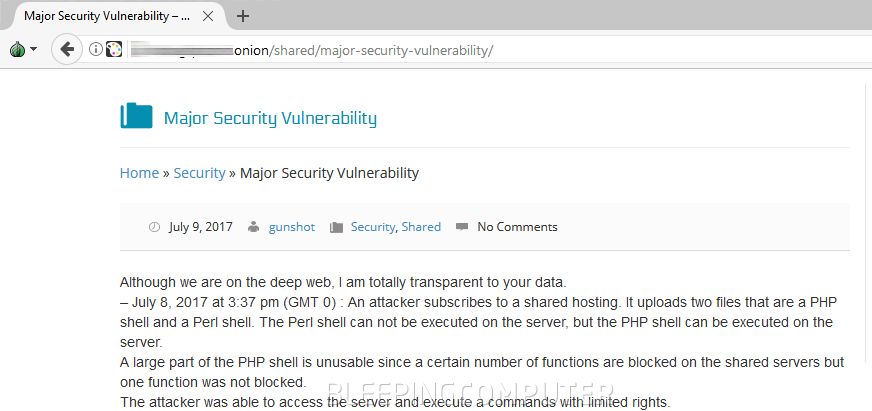
– July 8, 2017 at 3:37 pm (GMT 0) : An attacker subscribes to a shared hosting. It uploads two files that are a PHP shell and a Perl shell. The Perl shell can not be executed on the server, but the PHP shell can be executed on the server. A large part of the PHP shell is unusable since a certain number of functions are blocked on the shared servers but one function was not blocked. The attacker was able to access the server and execute a commands with limited rights.
– July 9, 2017 at 10:00 am (GMT 0) : Our experts detect intrusion. They export all created/modified files. All files are deleted.
– July 9, 2017 at 10:05 am (GMT 0) : The compromised server is passed in read only.
– July 9, 2017 at 10:06 am (GMT 0) : We begin to analyze the recovered files to understand the attack and damages.
– July 9, 2017 at 1:00 pm (GMT 0) : We identify the scenario of the attack. One PHP function was not disabled. We decide to apply a patch to all hosted sites to partition them all the more in their environment and we disable PHP function. We therefore reinforced the security of PHP.
– July 9, 2017 at 2:30 pm (GMT 0) : We change all passwords for all hosted sites (FTP and SQL) and the server is passed in read/write.“We believe that some sites have been exported,” Deep Hosting admitted at the end of their wiki page. “It is possible that the linked databases were also recovered.”
At least 91 Dark Web portals affected
Dhostpwned shared with Bleeping Computer a list of all the sites he managed to reach from the Deep Hosting server he initially hacked. The list includes 91 websites and is embedded at the end of this article.
The list includes all sorts of Dark Web services, ranging from drugs marketplaces to malware repositories, and from hacking forums to personal blogs.
“I hacked them,” Dhostpwned told Bleeping Computer in a private conversation today. “Their shared hosting was appauling [sic] in terms of security.”
“I’ve got the majority of files hosted from the site, all of their sql dbs,” the hacker added. “[sic] There was an assassination network hosted on it but i didnt end up getting into that since it was a vps hosted by them and they didnt have any sort of panel to access the vps.”
Hacker accidentally brings down Dark Web marketplace
On the other hand, Dhostpwned managed to gain access to other servers, including the one hosting the M.N.G Market, a marketplace that sold various illegal products. He uploaded the following text file in the server’s public root folder to prove his claim.
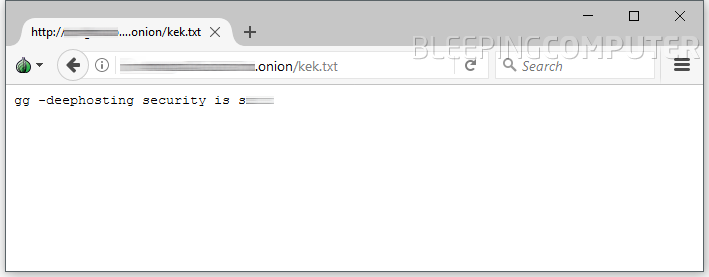
Moments after he uploaded his text file, the M.N.G Market went down, as Dhostpwned admitted to accidentally wiping their hard drive’s MBR.
According to Dhostpwned, the M.N.G Market team also used a VPS server to host their portal, but unlike others, had forgotten to change their default password for the VPS box.
This is not the first time a Dark Web hosting provider has been hacked. In February this year, members of the Anonymous hacker collective breached and dumped the database of the Freedom Hosting II free Dark web hosting service. They said they hacked the hosting provider because they found out that Freedom Hosting II knew customers were hosting child abuse forums on their service but did nothing about it. Freedom Hosting I was hacked for the same reason in 2011.
At the time of writing, Dhostpwned has not dumped any data from Deep Hosting or its clients. This might change in the future.
23mg64vxd2t6kurv.onion
27msssu6jaqhuk6m.onion
33qvlt5je5kif3jq.onion
3kqpypputjn2dhpp.onion
5ehtvrvuf2ef5h4h.onion
5xwgogyjnfcvrmvj.onion
654krjf5q6iupjot.onion
66xflun3ot54h6re.onion
6ccxadxrr4g3qm7d.onion
acteamwneyw3ik2w.onion
alphaor4wguil6wo.onion
anpbcfvqjg2txyw4.onion
aom6u55durkqpwaz.onion
assassinuyy7h425.onion
azo3mftev62hfckw.onion
azvjv2ji2ucukemz.onion
b6kbmmeh5qivsr47.onion
bzp2k3z63s4js3mo.onion
c7wgwx7zlmqntrm5.onion
cardobgwrjlzzqfl.onion
cbossftu5bjk5nx6.onion
ccguruetr5jwye5g.onion
cd2bkzxjx7vq3gxc.onion
cerberxypcgoxiw5.onion
clonedxpjlq5764s.onion
dc5clejbfoaxcqbk.onion
dhostov5qbwwyhcw.onion
dhwikikgqceifior.onion
dpanely75rdnw7yv.onion
dxke6tzygtgqvb6a.onion
e5nocpxm3rccdjeq.onion
e6wdnr4mcrzzefkt.onion
eurx66uednuvulfh.onion
feap5rllvmqi7lka.onion
g3n3bnjwhwokjco7.onion
g6ipitbghd6qutma.onion
gadmai6ebvzji6v6.onion
gbpoundzv2ot73eh.onion
gdbvx3pywrphpd5a.onion
hwikikijkk5g6acr.onion
iacwsvpfd4q43oer.onion
icloud4ho7bmn662.onion
imlz5jkbdcgl2c7s.onion
ji4qnwqney7siu2r.onion
jqcpeb5d77npwgyi.onion
k6sblsjcsgqpeym7.onion
kshdh4ipnl62xu2i.onion
lxhbgl43362zhmoc.onion
lxtrcj4uf3kxdhth.onion
mngmt4bouza7mobn.onion
mpt374ndlhhaxcsd.onion
mxs3tmyprhbne25m.onion
mz252nufkj42unlf.onion
n7gaof3th7hbktct.onion
nddgne7tasavd65z.onion
nfi3plp7famvohxm.onion
openwikicra5e6y2.onion
pacho2llwjm3c7ko.onion
q7ozu2gu7xt74gxk.onion
qyhaps2d7mzwwund.onion
rampshqaygkfwphb.onion
rj3herig755gboy5.onion
rothminhoy6dq45c.onion
scant2tnmpah5uao.onion
sholq4wfbybbzvj7.onion
shops64lgjykjrkp.onion
sux4lbtmxux5ou4f.onion
teekvknyeypyzpst.onion
teranovif5tsxdb6.onion
terrafmx663yli7u.onion
tgfc3mn2c6m6zga5.onion
tnmarkyzsx7xfbdg.onion
torwikica2juwzcg.onion
trinixy73gm6z4fq.onion
twiljiy37asd3t24.onion
ucdanzi5vdstr2gl.onion
unoppqar7cy3zvux.onion
vkzw2vhqqt7vvirr.onion
vn4bhyvlquetya7e.onion
vzpqzsukomqmlocz.onion
warezj5fngb44vn5.onion
webde3vkni6mhr3v.onion
xigjkusfkt2zvcvn.onion
xosnp3buimehxvma.onion
xwl45tkgnd7dv5ta.onion
y4rxzpod66bxgr4q.onion
zaoklnavsgzaxhf4.onion
zerodwbjcejayq7v.onion
zhqwte56j3xbnzdu.onion
zi5ivi3ufa7ijqys.onion
zoyel6xobic62353.onionSource:https://www.bleepingcomputer.com/news/security/dark-web-hosting-service-hacked-some-data-was-stolen/

Working as a cyber security solutions architect, Alisa focuses on application and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.











