Security researchers have uncovered fresh malware with hacking capabilities comparable to those of Pegasus, which was developed by NSO Group. The software, which is sold by an Israeli firm named QuaDream, has previously been used by customers to target journalists, political opposition leaders, and an employee of an NGO. The company that makes and sells the spyware is called QuaDream.
The malware was spread to the victims’ phones when the operators of the spyware, who are thought to be government customers, sent them an invitation to an iCloud calendar. The cyberattacks took place between the years 2019 and 2021, and the term “Reign” is given to the hacking program that was used.
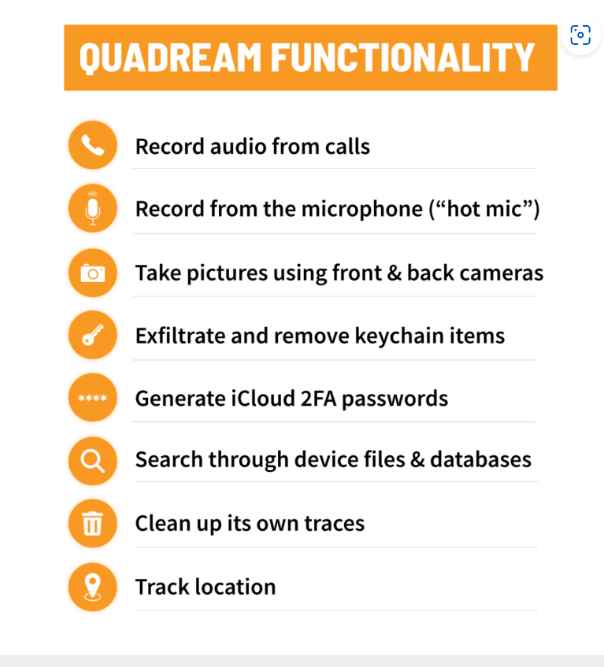
A phone that has been infected with Reign can, similar to a phone that has been infected with Pegasus, record conversations that are taking place near the phone, read messages that are stored on encrypted apps, listen to phone conversations, track the location of a user, and generate two-factor authentication codes on an iPhone in order to break into a user’s iCloud account.
Apple, which has been marketing its security measures as being among the finest in the world, has taken yet another hit as a result of the recent disclosures. It would seem that Reign poses an unprecedented and significant danger to the security of the company’s mobile phones.
The spyware that was built by QuaDream attacks iPhones by having the operators of the malware, who are believed to be government customers, issue an invitation to an iCloud calendar to the mobile users of the iPhones. Since the calendar invites were issued for events that had been recorded in the past, the targets of the hacking were not made aware of them because they were sent for activities that had already occurred.
Since users of the mobile phone are not required to click on any malicious link or do any action in order to get infected, these kind of attacks are referred to as “zero-click” attacks.
When a device is infected with spyware, it is able to record conversations that are taking place nearby by taking control of the recorder on the device, reading messages sent via encrypted applications, listening in on phone calls, and monitoring the position of the user.
The malware may also produce two-factor authentication tokens on an iPhone in order to enter a user’s iCloud account. This enables the spyware operator to exfiltrate data straight from the user’s iCloud, which is a significant advantage. In contrast to NSO Group, QuaDream maintains a modest profile among the general population. The firm does not have a website and does not provide any additional contact information on its page. The email address of Israeli attorney Vibeke Dank was included on the QuaDream business registration form; however, she did not respond to a letter asking for her opinion.

Citizen Lab did not name the individuals who were discovered to have been targeted by clients while they were using Reign. However, the organization did say that more than five victims were located in North America, Central Asia, south-east Asia, Europe, and the Middle East. These victims were described as journalists, political opposition figures, and an employee of an NGO. In addition, Citizen Lab said that it was able to identify operator sites for the malware in the countries of Bulgaria, the Czech Republic, Hungary, Ghana, Israel, Mexico, Romania, Singapore, the United Arab Emirates, and Uzbekistan.
In a security report that was published in December 2022 by Meta, the corporation that owns Facebook, the name of the firm was mentioned briefly. The report defined QuaDream as being an Israeli-based startup that was created by former NSO personnel.
At the time, Meta stated that it had removed 250 accounts on Facebook and Instagram that were linked to QuaDream. The company believed that the accounts were being used to test the capabilities of the spyware maker using fake accounts. These capabilities included exfiltrating data such as text messages, images, video files, and audio files.
The discovery of Reign underscores the continuous spread of very powerful hacking tools, even as NSO Group, the developer of one of the world’s most sophisticated cyberweapons, has received intensive investigation and been banned by the Biden administration, likely limiting its access to new clients. NSO Group is the maker of one of the most advanced cyberweapons in the world.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











