Authorities arrest multiple Egregor ransomware hackers
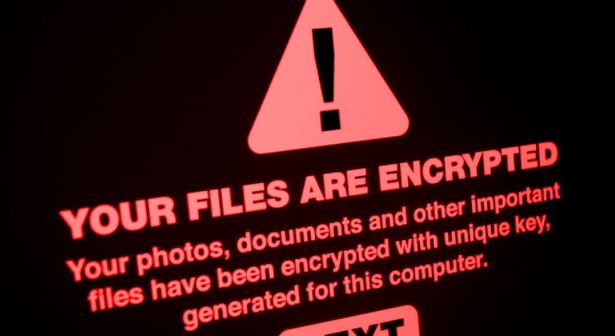
Recent reports indicate that the joint work of the French and Ukrainian authorities led to the arrest of multiple individuals accused of belonging to the Egregor ransomware group. Operators ofRead More →