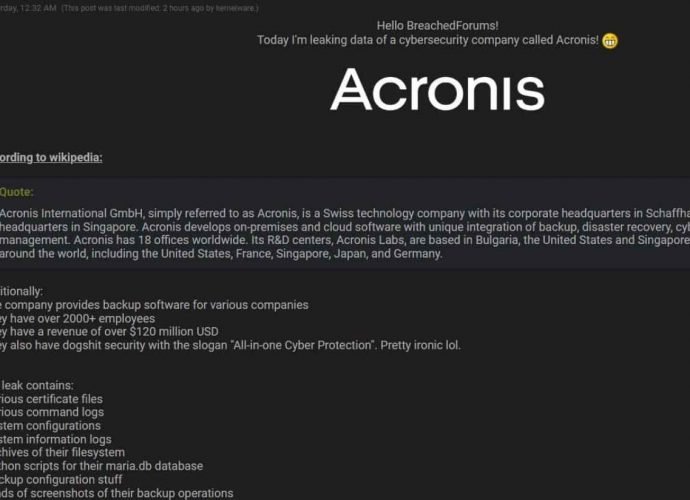
Why famous cyber criminal forum Breach Forums has been closed down forever?
Breach Forums, a notorious site for hackers and cybercriminals, has been closed down forever. Conor Brian Fitzpatrick (as Pompompurin, nicknamed Pom), the owner, creator, and administrator of Breach Forums, wasRead More →