Hack Windows, Android, Mac using TheFatRat (Step by Step tutorial)
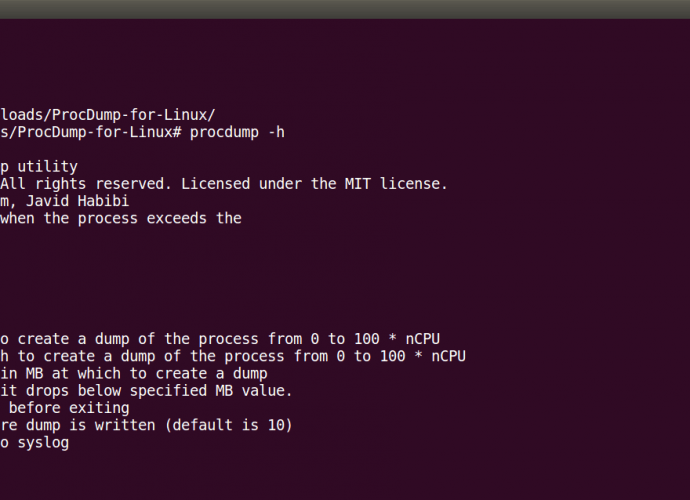
Using Metasploit is not an difficult thing anymore. Because there are many resources that are available over the internet. Which tells usage of metasploit. Metasploit are the common ways ofRead More →