PROCESS DOPPELGÄNGING – GIVING HARD TIME TO AV VENDORS
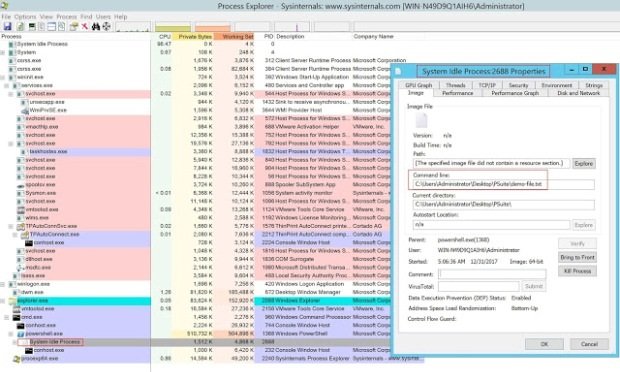
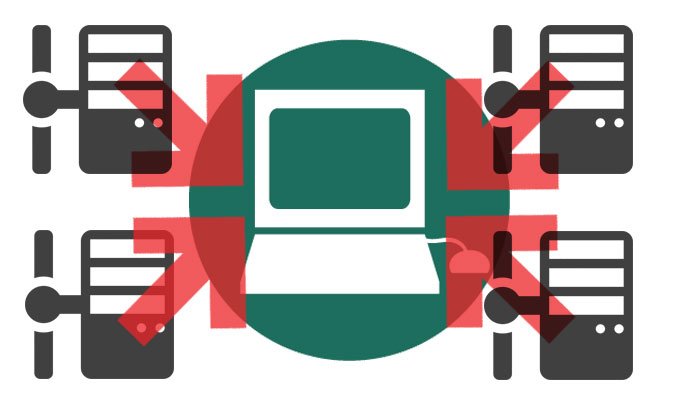
Recently security researcher’s from enSilo group presented new evasion technique called Process Doppelgänging at Blackhat Europe-2017. This technique bypasses most popular Antivirus, NGFW and EDR solutions present in the market. This techniqueRead More →