As the values of the largest cryptocurrencies have multiplied, so too have reports of digital-currency miners stealing resources to increase the profitability of their operations. Few weeks back, we reported that the world’s largest oil-pipeline company discovered unauthorized digital-currency mining happening on the company’s hardware. Also, Cryptocoinsnews pointed out that a Starbucks in Buenos Aires had its wi-fi hacked to force a 10 second delay when connecting so it could mine Monero – currently the world’s 11th largest cryptocurrency – with people’s laptops.
Ricky Jais, cyber security expert working with International Institute of Cyber Security IICS noticed something wrong with the ecommerce website of one of the largest retailer in Mexico LIVERPOOL, www.liverpool.com.mx.
Ricky visited the online shopping website of Liverpool for some online shopping where is discovered that the module of invoice (facturacion) was sending some traffic to coinhive.com. The website forces the website visitor to coinhive and then uses the user computer CPU to mine digital currency without taking permission from website visitor. CoinHive, works with Monero, a digital currency like bitcoin. Coinhive is optimized for CPU mining that recently hit a new all-time high above $300, and has surged over 1,500% this year so far, according to data from CoinMarketCap.
WEBSITE VISITOR CPU USAGE BEFORE OPENING THE WEBSITE
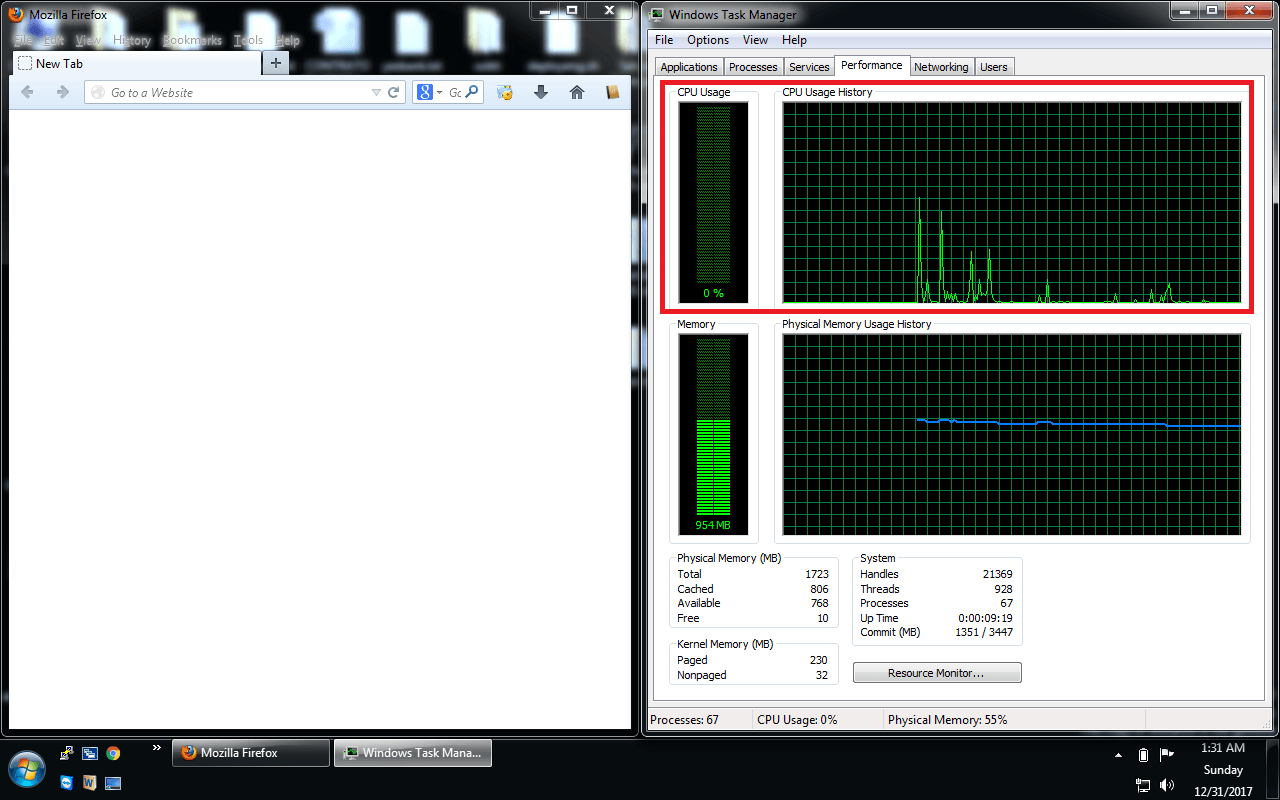
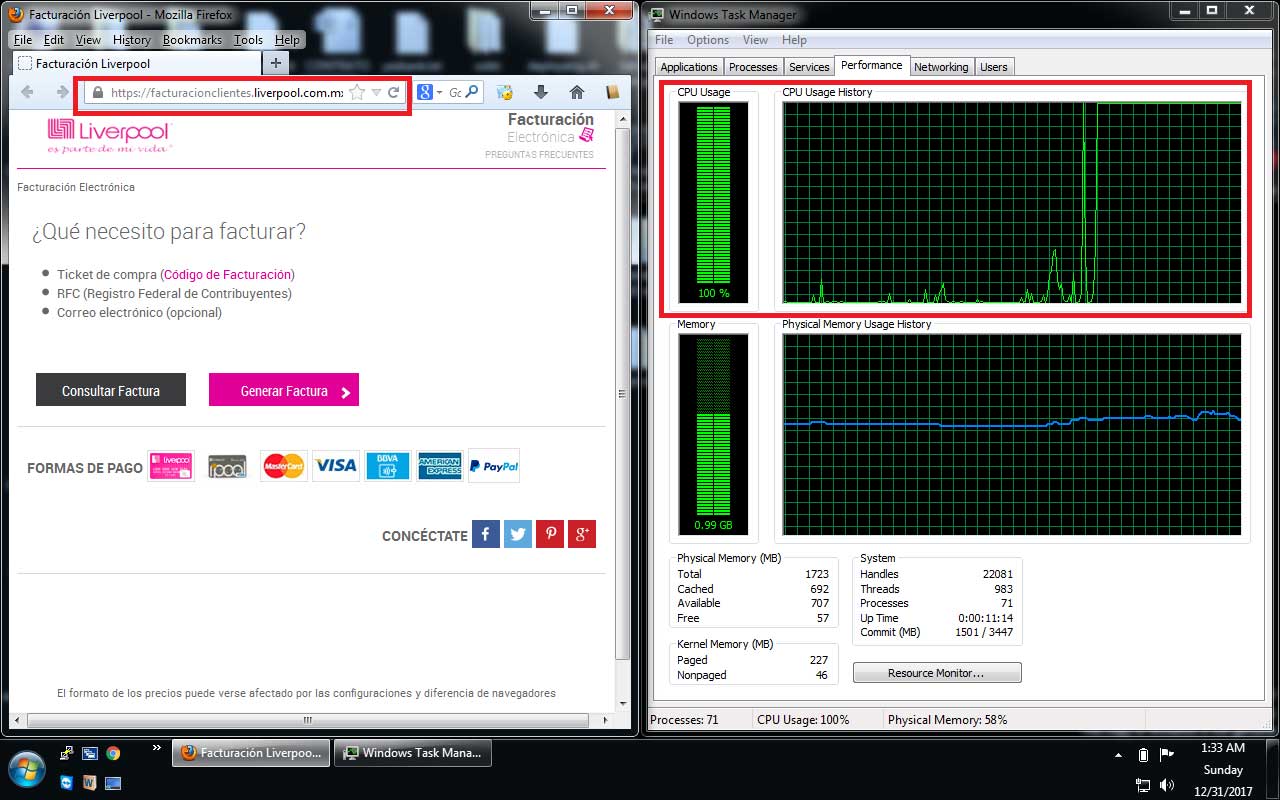
The website injects a visitor’s browser with code that hijacks their processing power to generate digital currency. This process, known as “mining,” is resource-intensive and can significantly impact performance as shown in the image below.
WEBSITE VISITOR CPU USAGE AFTER OPENING THE WEBSITE
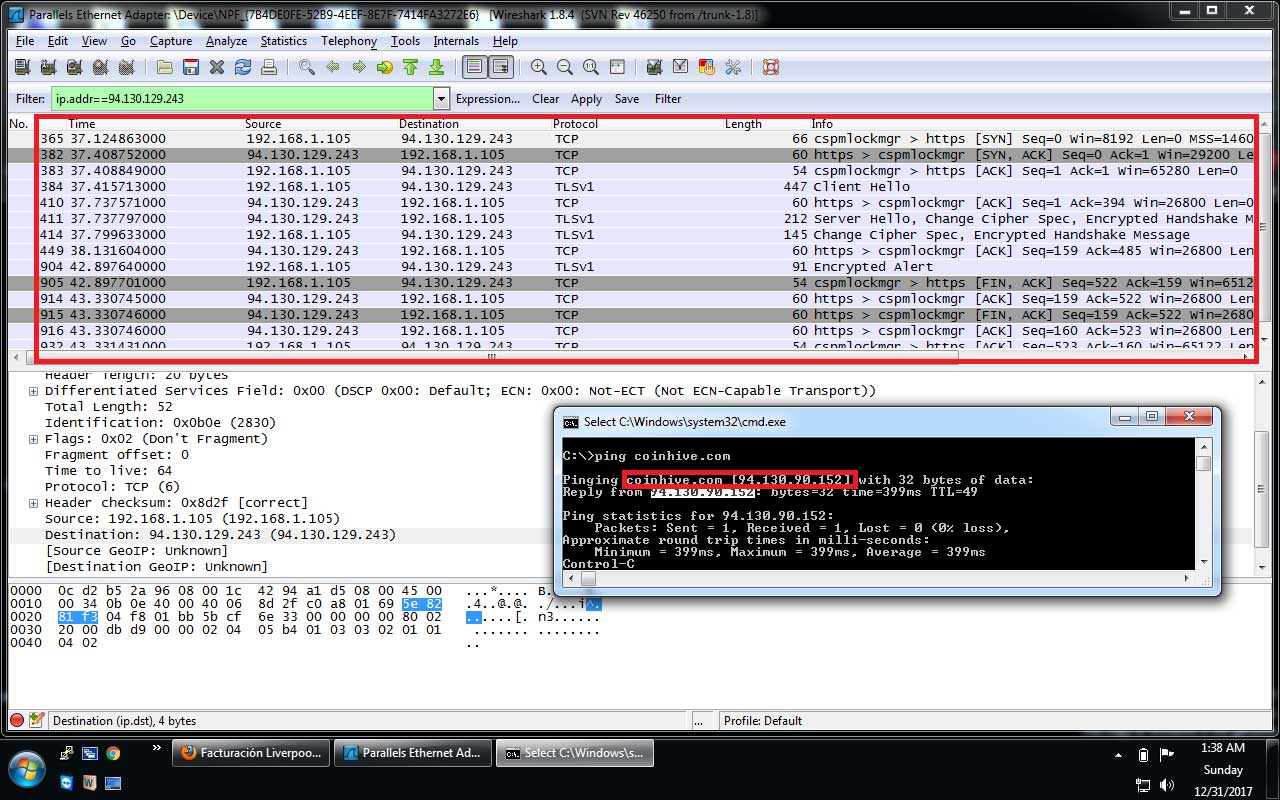
On further debugging the website is taking the visitor to the IP address (94.130.90.152) which belongs to coinhive.com
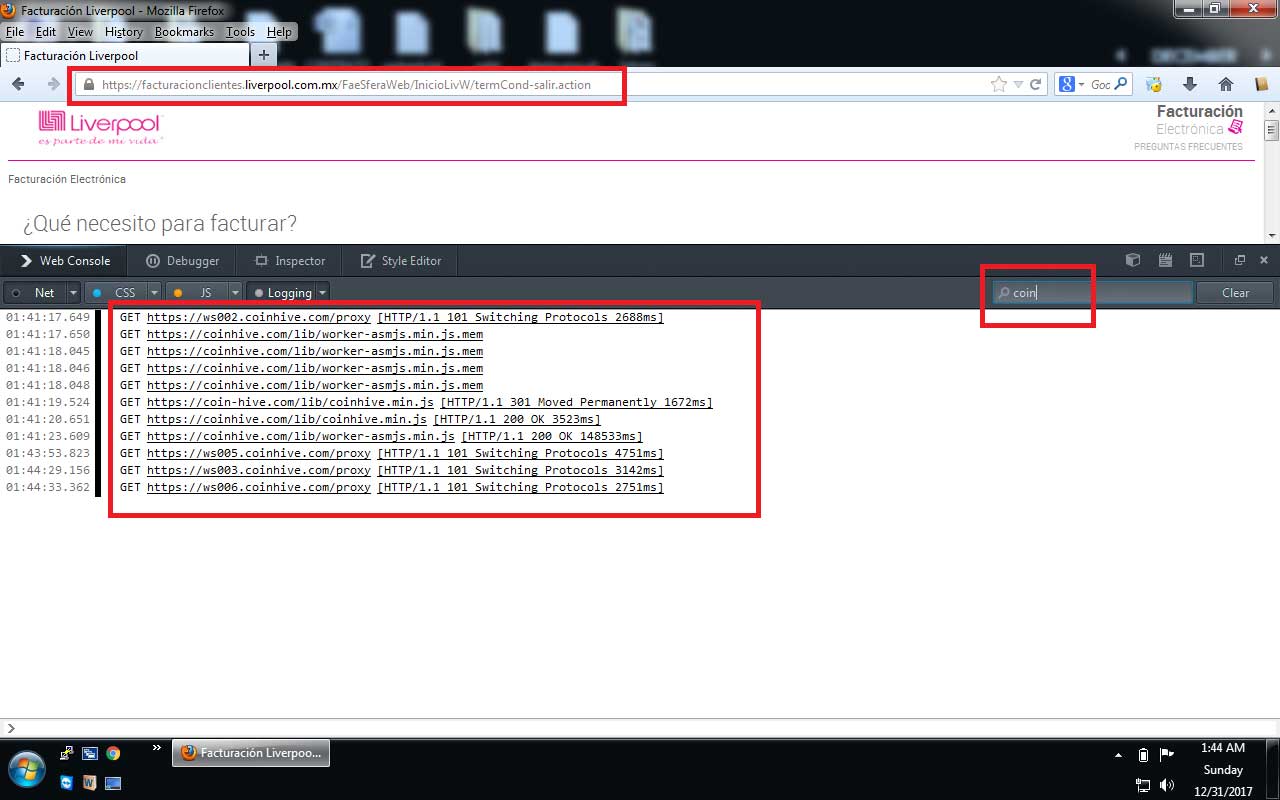
Next level of analysis reveled that the website (https://facturacionclientes.liverpool.com.mx) injects the code in the website visitor’s browser to hijacks their processing power to generate digital currency as shown in image below.
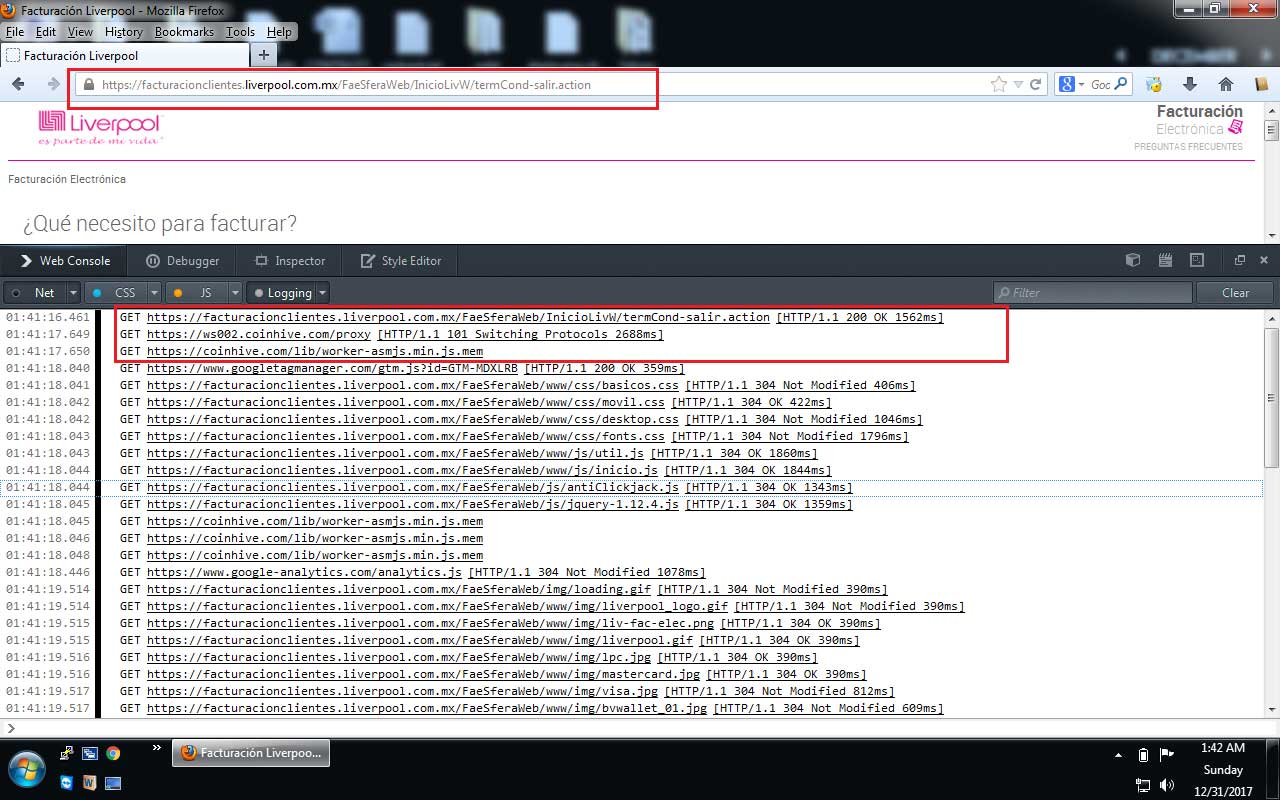
The inject code continuously poll coinhive links as shown below
[“ws001.coinhive.com/proxy”, “ws002.coinhive.com/proxy”, “ws003.coinhive.com/proxy”, “ws004.coinhive.com/proxy”, “ws005.coinhive.com/proxy”, “ws006.coinhive.com/proxy”, “ws007.coinhive.com/proxy”, “ws029.coinhive.com/proxy”],
[“ws008.coinhive.com/proxy”, “ws009.coinhive.com/proxy”, “ws010.coinhive.com/proxy”, “ws011.coinhive.com/proxy”, “ws012.coinhive.com/proxy”, “ws013.coinhive.com/proxy”, “ws014.coinhive.com/proxy”, “ws030.coinhive.com/proxy”],
[“ws015.coinhive.com/proxy”, “ws016.coinhive.com/proxy”, “ws017.coinhive.com/proxy”, “ws018.coinhive.com/proxy”, “ws019.coinhive.com/proxy”, “ws020.coinhive.com/proxy”, “ws021.coinhive.com/proxy”, “ws031.coinhive.com/proxy”],
[“ws022.coinhive.com/proxy”, “ws023.coinhive.com/proxy”, “ws024.coinhive.com/proxy”, “ws025.coinhive.com/proxy”, “ws026.coinhive.com/proxy”, “ws027.coinhive.com/proxy”, “ws028.coinhive.com/proxy”, “ws032.coinhive.com/proxy”]
Another recent case similar to this is when one or more malware creators made around $63,000 in five months by invading unpatched IIS 6.0 servers to install their miners. To install the miner, they first hijacked the servers by exploiting the CVE-2017-7269 vulnerability: a good example of the importance of keeping up with patches.
In a way, anybody doing some online shopping at an online portal or taking out invoices should be careful as it’s a intelligent way of mining cryptocurrency and to generate revenue. In another, more salient way, it’s completely invasive and inappropriate.
HOW TO PREVENT THIS?
Watch your CPU: Check Activity Monitor on a Mac or Task Manager on Windows. If your computer has fans, you might hear them revving up to deal with the extra heat generated by a heavily loaded CPU chip.
Watch your network traffic: You can install free network monitoring software, which can help you to see which websites your computer is opening at backend, or IPs your computer is connecting to.
Consider software to control JavaScript: According to professor of ethical hacking course of International Institute of Cyber Security, NoScript, a popular free tool can help you to keep control over intrusive JavaScript, Flash, and Java in your browser.
Install an anti-virus that detects coin mining code or website: For example, AVAST products classify browser-based coin miners as malwares and can be block some coin miner code easily.
Cyber Security Education: IT managers or computer users can take cyber security courses which can teach them how to protect their IT infrastructure or personal computers from hackers.
Patch your IT infrastructure: Hackers can breach into your servers and install cyptomining code to leech ‘free money’ from all your website visitors, leaving you to bear the brunt of any complaints. Thus it is always recommended to patch your servers.
Next time you visit any website make sure your consider above recommendations to save yourself from hackers.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.












