3 Linux & macOS Hacking Tools Developed By CIA Exposed: Achilles, Aeris, SeaPea
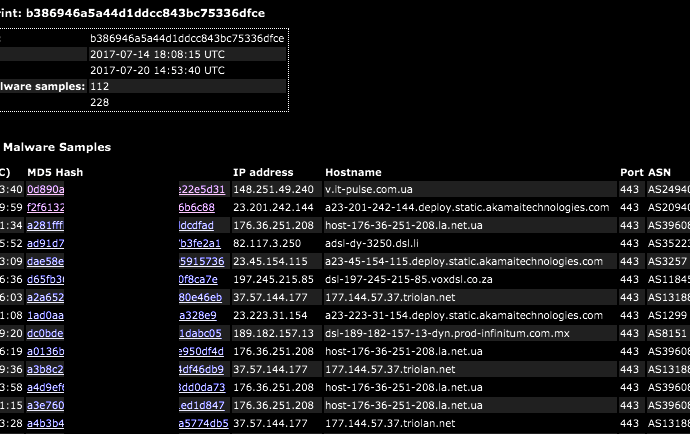
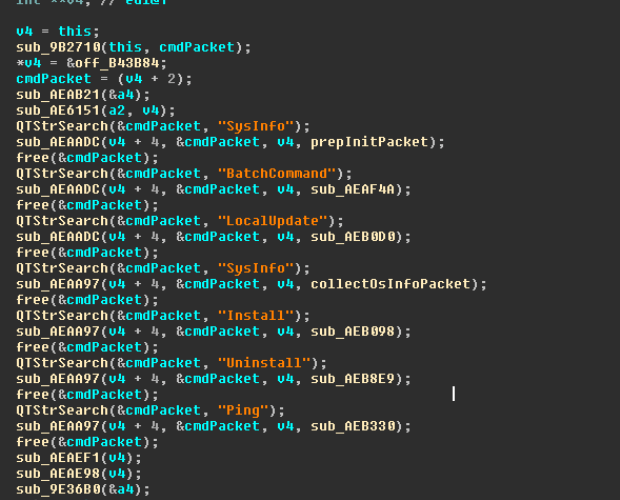
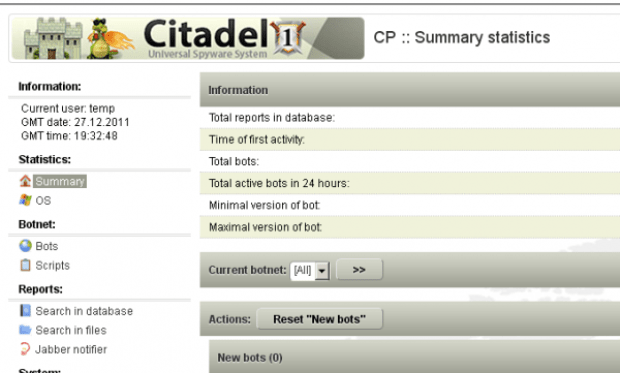
Short Bytes: Continuing the ongoing Vault 7 leaks, WikiLeaks has exposed more CIA-developed malware. Leaked malware includes Aeris, which is an automated implant for infecting Linux systems. The other two malware, namedRead More →