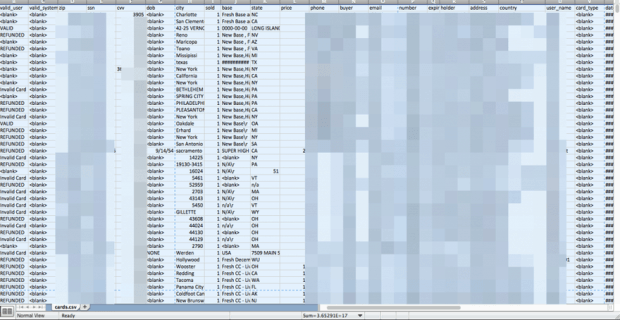
100 million credentials from the Russian Facebook VK.com go on sale
100 million login credentials belonging to the users of the Russian social networking platform VK.com (VKontakte) are available for sale on the Dark Web. Another day another data breach, thisRead More →