Marine Corps Cyberspace Warfare Group, the new hacker unit
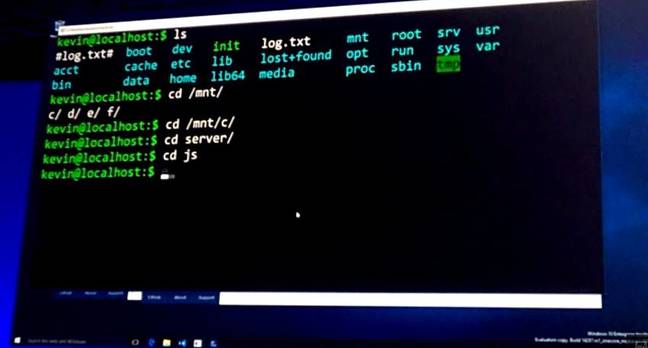
The United States Marine Corps has launched on March 25th a new hacker support unit named Marine Corps Cyberspace Warfare Group. It is unnecessary to remind the importance of cyber capabilitiesRead More →